Contents
- What is a Secret Sharing Scheme?
- Why is Secret Sharing needed?
- What is Shamir's Secret Sharing?
- How does Vault12 use Shamir's Secret Sharing?
- Part 1: The Cryptography behind Vault12 with Terence Spies
- Part 2: The Cryptography behind Vault12 with Terence Spies
- What is the importance of Shamir's threshold number of shares?
- Shamir's Secret Sharing allows your secrets to be both Secure and Dynamic
- Should you decentralize custody of your secrets?
Understanding Shamir’s Secret Sharing (SSS)
This article describes a well-known strategy for distributing shared secrets: Shamir's Secret Sharing.
What is a Secret Sharing Scheme?
In cryptography, secret sharing schemes are schemes that split shares of a given secret among a set of trusted recipients. For example, this secret might be a very important piece of information that is needed in the future, but meanwhile needs to be kept private and secure. Each share is completely useless on its own, but when combined, the shares reconstruct and display the secret. As a thought experiment: think of secret sharing schemes as a puzzle where the puzzle pieces are split among ten players but are completely blank. The image that the puzzle can create only appears once all the pieces are put together.
Why is Secret Sharing needed?
The kind of data that is best suited for a secret sharing algorithm is information that must be kept absolutely private, but must also be stored securely and never lost. Typically, you'd use secret sharing for access keys to accounts with highly sensitive information in them. The goal is to spread the key out from one geographic location into multiple — so that in order to compromise a system, you'd first need to compromise devices in several distinct locations. There are multiple kinds of secret sharing algorithms: the one we'll be discussing is Shamir's Secret Sharing (SSS).
What is Shamir's Secret Sharing?
Adi Shamir's scheme is a securely encrypted secret sharing scheme that requires some or all participants to reconstruct a secret. Shamir's Secret Sharing allows for a hierarchical schema where some participants may be more trustworthy than another. For example; when running Shamir's scheme for a private key and sharing it among friends and family, one could grant family members greater authority in the scheme and friends lesser authority in the scheme.
How does Vault12 use Shamir's Secret Sharing?
In Part 1 of the video below, well-known security expert Terence Spies explains how the fundamentals of Shamir's Secret Sharing operate, and how its cryptography is used in the Vault12 system.
Part 1: The Cryptography behind Vault12 with Terence Spies
Part 2 of the video explains how advanced concepts such as Thresholds work to give Vault12 a streamlined experience.
Part 2: The Cryptography behind Vault12 with Terence Spies
What is the importance of Shamir's threshold number of shares?
Considering the nature of how Shamir's scheme is built, a threshold parameter can be specified during the creation of the scheme. Instead of requiring that every single share is present to reconstruct a key like a puzzle, Shamir's scheme requires a threshold number of shares. The value of this threshold is at the discretion of the secret sharer. The secret sharer could choose to require every single share for reconstruction of the key or three-quarters of all shares held by participants.
Shamir's Secret Sharing allows your secrets to be both Secure and Dynamic
Shamir's Secret Sharing has the following properties:
- Secure: Shamir's scheme is cryptanalytically unbreakable in its encryption model in that no holder of a share can uncover the shared secret without first gaining access to the threshold number of secret shares. The secret will be kept absolutely secure and confidential from participants in the scheme. Only the secret sharer will see the original data from the deconstruction and reconstruction of the data.
- Dynamic: The scheme allows for a secret owner to amend the rules of a given secret securely. This means a person sharing a secret among a set of participants could use their status as the secret owner to create more splits of a key and distribute those to more participants if he or she so chose. Or, the secret owner could remove some participants remotely from the scheme — all while leaving the other participants in the secret sharing scheme completely unaffected.
Should you decentralize custody of your secrets?
Using an application built on Shamir's Secret Sharing doesn't imply that it's the perfect layer of security for the storage of all secrets in all cases — rather, it responds to a specific situation that is suitable for decentralized and trusted custody of a specific secret.
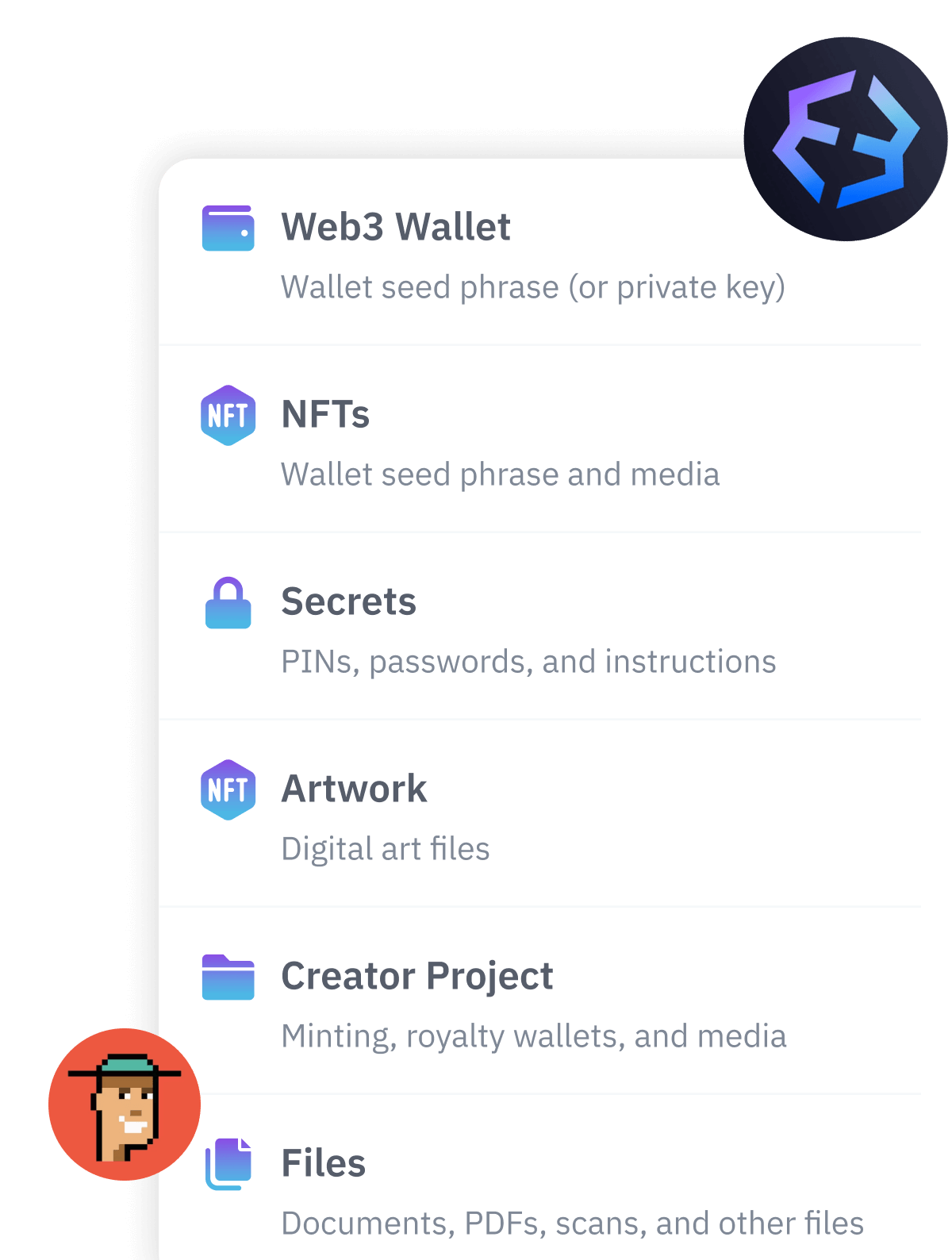
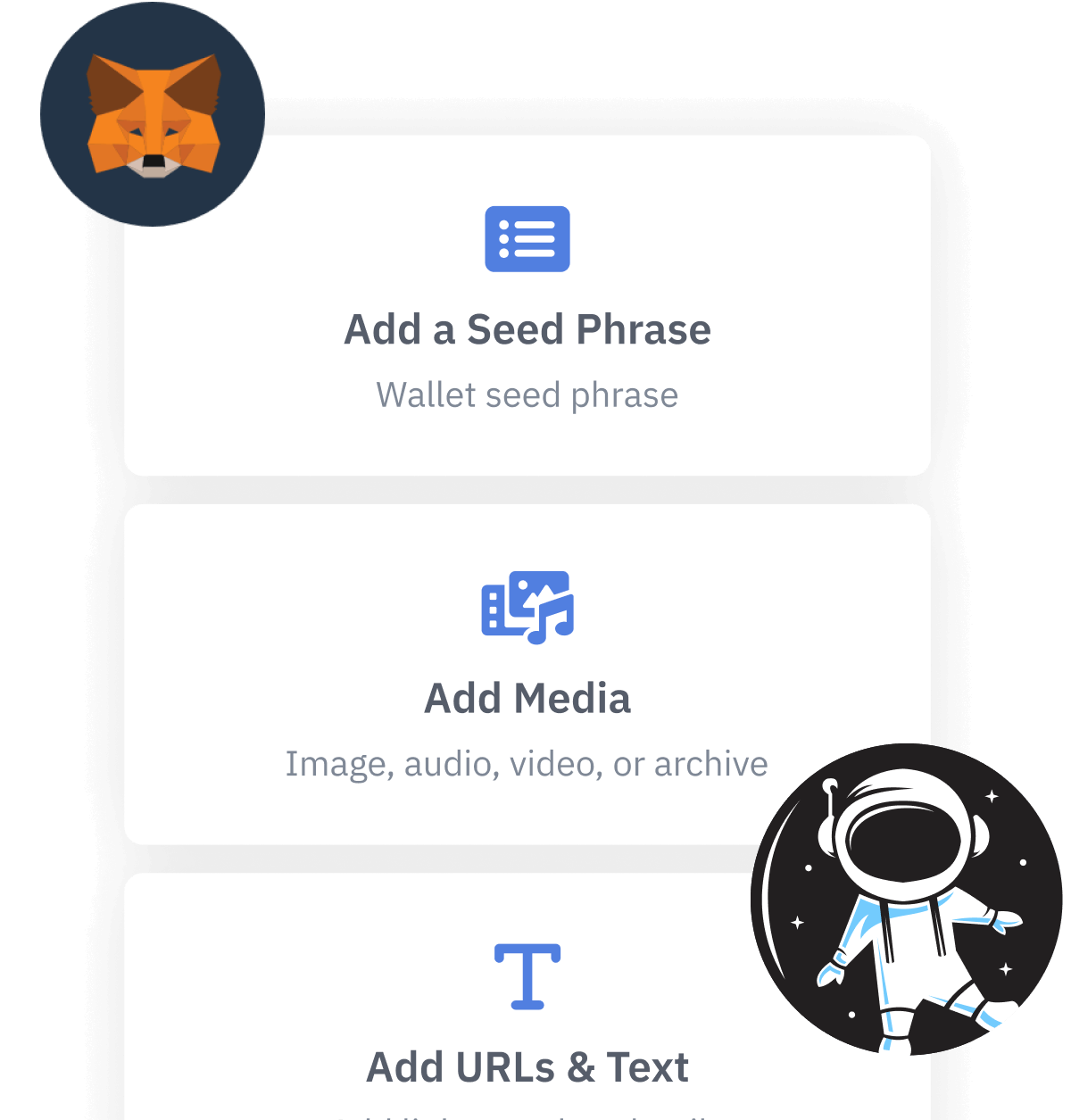
At Vault12, we think that the best-suited specific secrets for which to utilize Shamir's Secret Sharing are private keys to cryptocurrency balances, and seed phrases for the recovery of wallets. To that end, Vault12's mobile app implementation of Shamir's Secret Sharing - Vault12 Guard - lets users assign friends and family as guardians of their secrets.
Shamir's Secret Sharing is an intriguing cryptography scheme that is useful for decentralizing custody of sensitive data. However, it is not suited for the maintenance of just any secretive data. Since the scheme entails assigning participants to store shares of a secret, these participants need to be trusted. While the encryption scheme renders it impossible for participants to derive anything from the share they receive, multiple participants could collude together to meet the threshold requirement of shares and uncover that secret. Therefore, it is important that the people that you share a secret with using Shamir's Secret Sharing are trustworthy.
For more details about Vault12's innovative technologies, visit the Vault12 Technology page.
Understanding Shamir’s Secret Sharing (SSS)
This article describes a well-known strategy for distributing shared secrets: Shamir's Secret Sharing.

Blake Commagere
Blake is a serial entrepreneur, angel investor, and advisor to several companies in the SF Bay Area. He has started seven companies and sold five of them. He regularly gives talks on subjects including Growth Hacking, Fundraising, and Psychology Management.
He created the social gaming category by building some of the biggest apps ever (over 50 Million players) on Facebook, including the iconic games Zombies, Vampires, and Werewolves. Blake also wrote and designed the first version of Causes on Facebook, which has over 120 Million users and has raised over $100 million for various charities. Blake graduated with a Bachelor's degree in Computer Science from Rice University.

Max Skibinsky
Max Skibinsky is a serial entrepreneur, angel investor, and startup mentor. Most recently, Max was an investment partner with Andreessen Horowitz, where he focused on enterprise security and bitcoin and deals with Tanium, TradeBlock, and Digital Ocean. In addition to co-founding Vault12, Max leads the R&D team. Before that Max was the founder and CEO of Hive7, a social entertainment company that became part of The Walt Disney Company. In 2003, Max joined the newly formed Voltage Security, an encryption startup incubated at Stanford University, where he architected and designed an Identity-Based Encryption messaging system that was showcased at DEMO '04. Voltage was acquired by Hewlett Packard in 2015. Max has also advised and invested in many startups graduating from Y Combinator including Eligible, Transcriptic, and ZenPayroll. Max graduated with a masters' degree in theoretical and mathematical physics from Moscow State University.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
Vault12 is NOT a financial institution, cryptocurrency exchange, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys for the purpose of inheritance. We provide no legal or financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
You will lose your Bitcoin and other crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.