Contents
- Key Highlights: Using a VPN for Crypto Security
- What is a VPN? A high-level view of the technology
- Who uses VPNs?
- When should crypto consumers use VPN software?
- How much privacy do VPNs offer?
- How to choose what VPN is best for crypto
- Limitations or risks of using a VPN
- Other forms of VPN
- VPN Alternatives
- Should you use a VPN for crypto?
VPNs for Crypto: How to increase your crypto security
Virtual Private Network (VPN) software makes it harder for your crypto activities to be observed
When it comes to cryptocurrency, it's important to take steps to safeguard your online activities in order to protect yourself and your assets. Using Virtual Private Networks (VPNs) for crypto activities can help. VPNs have the benefit of providing an additional layer of security, but there are limitations. This article explains what VPNs can and can't do for you.
Key Highlights: Using a VPN for Crypto Security
- Privacy: VPNs increase your online privacy by hiding your location from websites you visit, and hiding websites that you visit from your ISP. However, VPNs can not offer complete privacy, and VPN usage data could be subpoenaed.
- Usability: VPNs may reduce your speed and convenience.
- Security: VPNs can potentially be hacked, and while using them you are still susceptible to malware and other online threats.
- Legal risks: Some governments prohibit and take steps to identify and/or block the use of VPNs.
- It is not recommended to use free VPNs from commercial companies (they are making money somehow, maybe with ads, and likely from selling usage data).
What is a VPN? A high-level view of the technology
A Virtual Private Network (VPN) is software that encrypts your online data and sends it through a different computer, making it more difficult for anyone to see what you are doing online. This increases both your security and privacy.
A VPN's layer of encryption offers added security. For example, if you connect to an unencrypted service (like a web site that uses http instead of https), or a weakly-encrypted service (even an https web site may have weaknesses in its configuration), the VPN's encryption will help to prevent eavesdroppers on the network from being able to see your traffic.
Because the VPN connection "wraps" and sends your data through a different computer (the VPN server) you also gain privacy: sending your data through this "secret tunnel" limits how much of your online activity your internet service provider can observe. And the destination internet service that you are connecting to is also prevented from seeing your home IP address or physical location - instead, your internet traffic looks like it is coming from the VPN server that you are tunneled through.

Using a VPN protects against some prying eyes
Who uses VPNs?
People use VPNs for many reasons. They might want to:
- add a layer of encryption as protection against eavesdroppers while they use an untrusted wireless network.
- connect securely to their employer's network in order to gain access to a service or machine on an internal work network.
- pretend that they are in a different location in order to get around rules (for example, some online services limit the countries that they serve).
- hide their activities from their internet service provider.
- hide their activities from governments or the police.
Ultimately, VPNs increase data protection and privacy, for legitimate or illegitimate reasons.
When should crypto consumers use VPN software?
Since its inception, cryptocurrency has prioritized the importance of user privacy. The Bitcoin White Paper dedicated its Section 10 to "Privacy," clearly separating the concept of a crypto user's identity from their publicly-visible transactions.
If others find out that you own cryptocurrency or other digital assets, or that you use a particular software or hardware wallet, it may be more likely that you would be targeted for theft or hacking. You may not want your ISP to know that you connect to crypto exchanges, or that you have a habit of checking crypto prices. You may not want a crypto exchange to know what country you are in, or to have any information about your IP address or location.
Moving into the future, the unpredictability of laws and restrictions that may be placed on cryptocurrency by different jurisdictions makes some crypto owners understandably hesitant to share any more information about their transactions than they have to.
It is recommended that privacy-conscious crypto users use a VPN when they connect to any crypto-related web site or service.
How much privacy do VPNs offer?
Although VPNs offer more privacy from the ISP and from the service that is consumed, the VPN service provider will still have logs that can identify where the user connected from. (If the user pays for service from the VPN provider, that provider likely also has additional personal information about the user as well.) There may also be some logging on the VPN provider's machines that captures destination addresses (for example, unencrypted web site URLs could be logged by the VPN provider). So VPNs do not offer perfect privacy - but they do reduce the audience of people who could analyze your internet traffic.
Increased privacy does not suggest complete anonymity: if you use a VPN to log into a web site with an account that is associated with your contact details, of course, the site still knows that it is you, even though they would not know what your location is.
How to choose what VPN is best for crypto
Here are some of the things that you should consider when deciding which VPN service to use:
- Generally, avoid free services that are provided by commercial businesses. They are making money somehow. (Open source software can be excellent and free, since it avoids this conflict of interest of needing to make money.)
- Look for a VPN provider that states their respect for your privacy. They should be transparent about what logging they do, and they should state that they do not resell their customers' personal information.
- Look for a VPN provider that is based in a country with strong privacy laws, for example, Switzerland (with ProtonVPN), Panama (with NordVPN), the British Virgin Islands (with ExpressVPN), and the Netherlands (with SurfShark).
- Don't rule out VPN providers from countries with "stronger-than-average" privacy laws, and with a strong stated commitment to user privacy (like MullvadVPN in Sweden).
- Your VPN provider should offer VPN connection servers that are hosted in the locations where you would like to appear to be from.
- Ensure that your VPN provider supports the device platforms that you need.
- VPN providers should be able to state that they have received an independent security and privacy audit by an industry-respected security organization.
- It is a nice feature if they accept payment in cryptocurrency. (If you can pay in crypto, you do not have to share as much information about your identity.)
Limitations or risks of using a VPN
There are a few downsides to consider when using a VPN for crypto or for any general purpose.
Using a VPN will probably slow down your connection speed.
Some online services may block your access if they detect that your IP address is associated with a VPN. You might be able to evade the block by connecting to a different server from your VPN provider's fleet, and you may not ... "VPN blocking" will be an occasional inconvenience.
Some governments take measures to block the use of VPNs entirely, in an attempt to limit communication and privacy. Because of this, it is much more difficult to use VPNs in a few countries in the world. The legality of VPN use in countries that ban or otherwise prevent the use of VPNs is something that you should research and consider carefully if you will find yourself in that situation.
VPNs will not protect your machine from malware - that is not its purpose. You still have a responsibility to follow all guidelines for sensible internet security.
Web sites can still leave cookies and other privacy-related breadcrumbs on your local computer. You should clear your browsing history after online activity if you would like to increase your privacy more.
Even if a VPN provider claims to limit their logging of your traffic, they can potentially be compelled to provide traffic logs if given a court order.
Like every other company, VPN providers can be hacked or have data breaches. If a VPN provider's access logs are unintentionally published, any information that they do have about you may be leaked. This has happened to several VPN providers, including LimeVPN and UFOVPN.
Other forms of VPN
Instead of running conventional VPN provider software on your laptop and mobile devices, you could install a VPN client in a different form, like on a wireless internet router, although that setup can be tricky and inconvenient.
There are also browser extension VPNs that only protect data that is transmitted through a specific browser, although many people find the scope of such a partial VPN tool to be too limited.
There is also a new breed of decentralized, open-source VPNs that are entering the market, like mysterium. Although these VPNs offer intriguing technology, they do not yet have a large user base or a long a track record like conventional VPNs, and are not yet as user-friendly.
VPN Alternatives
Apple announced with iOS 15 that it is offering a new privacy tool for iCloud users in the form of a Safari browser feature called Private Relay. While not a VPN, it does add a layer of encryption, and it does mask the user's IP address (although it does not evade geoblocking controls, so you can not pretend to be in a different location).
Cloudflare offers a VPN alternative called "1.1.1.1 Warp." This service acts as a DNS resolver that can cloak what internet-based services you are connecting to from your Internet Service Provider. The service that you are connecting to, however, will still see your actual IP address.
Alternatively, you could also choose to use an open source peer-to-peer browser like Tor. Tor is not a VPN, but the Tor network breaks data up into smaller pieces and individually routes them through nodes that can be run by anyone, making it nearly impossible to reassemble who did what. Tor traffic can be quite slow, and may be blocked by service providers more than standard VPNs.
Should you use a VPN for crypto?
Although nearly all crypto-related web sites and internet services already provide a high level of security by protecting "in-flight" data with HTTPS/TLS encryption, you might not want the web site that you are connecting to to know your location or IP address, and you may not want your ISP to have visibility into your online habits. If you want to add another layer of security and privacy to your crypto activity, using a VPN can help.
So when should you enable your VPN? Some people leave a VPN tunnel enabled all of the time, and only disable it temporarily if they find that they are blocked from using a particular service. Others only enable their VPN before connecting to a cryptocurrency exchange where they want to transact cryptocurrency. Some cautious users will not even connect to a crypto price site without using a VPN (since that could tip your ISP off to the fact that you care about crypto prices). As with so much in cryptocurrency, the choices are up to you - but it is highly recommended that you have a VPN and that you know how to use it, so that you can make informed and appropriate decisions. Empower yourself with some experience using a VPN so that you can enable it when you feel it's prudent.
VPNs for Crypto: How to increase your crypto security
Virtual Private Network (VPN) software makes it harder for your crypto activities to be observed

Art Krotou
Art is a crypto-security expert and researcher with serial entrepreneurship background. Having a degree in physics and experiences in multiple cutting-edge industries like fintech, secure hardware and semiconductors, and identity gave him a unique multi-faceted perspective on the problem of key management for individuals in the crypto networks and the evolution of the internet in general.
In his current work, he is specifically researching how cryptographic keys can be inherited without posing a threat to 3rd parties in edge cases. In addition, he advocates for "fault-tolerance via secrets automation". He discusses the quantitative impact of user experience factors on the uptake of non-custodial solutions.
As one of his most notable accomplishments, he co-founded and led through the early years of the company that contributed to the complex technology behind Apple's recent M-series CPUs. He is also the creator of the most friendly and aesthetically pleasing, but nonetheless super secure and fault-tolerant hardware wallet - U•HODL.
Check out his curated series of "Vault12 Learn" contributions below, and follow him on Twitter and LinkedIn for more sharp insights.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
You will lose your Bitcoin and other crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
DISCLAIMER: Vault12 is NOT a financial institution, cryptocurrency exchange, wallet provider, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys. We provide no financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
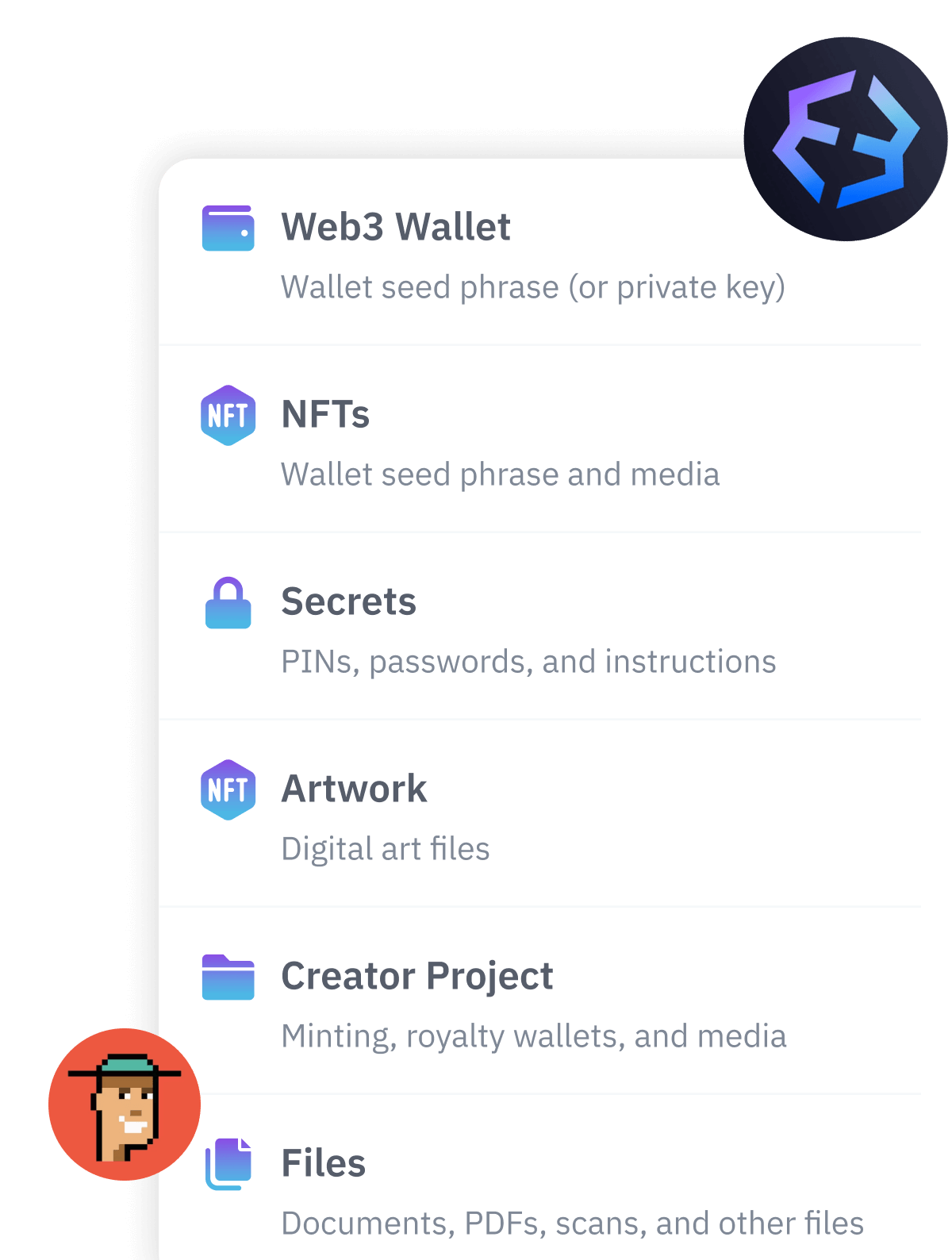
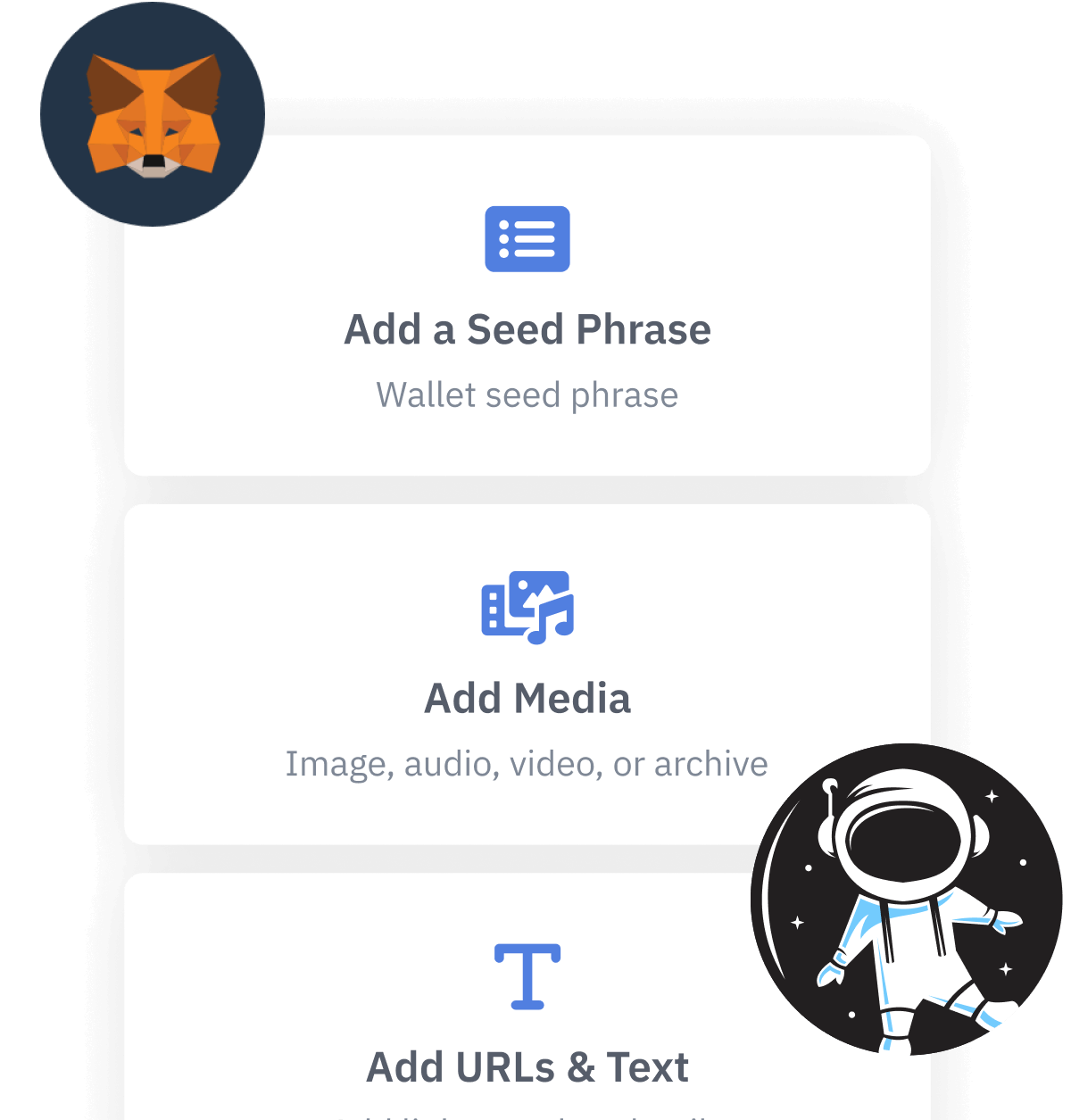
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.