Contents
What Is a Self-Sovereign Identity?
Personal control over our online personas has given rise to the philosophy of self-sovereign identity (SSI). In essence, a person who has an SSI has sole ownership of their digital and analog identities and controls how their data is viewed or shared.
Summary
Personal control over our online identities and personal data has given rise to the philosophy of self-sovereign identity (SSI). In essence, a person who has an SSI has sole ownership of their digital and analog identities, as well as control over how their personal data is used or shared. While the concept of SSI has existed for decades, it wasn’t until the advent of blockchain that this concept could be translated into a real-world application.
As a growing proportion of our lives moves online, the number of accounts, user profiles, and login credentials the average person needs to manage is continually expanding. As more and more organizations establish their own proprietary system for verifying their users’ identities, end users end up with a multitude of online personas owned by various online organizations. Within this structure, online identities currently suffer from three persistent issues:
- Lack of Flexibility: Because most existing online identity systems are based on business relationships and technical integrations to centralized authorities, these identity systems are rigid and can only be applied to narrow, predetermined use cases.
- Questionable Privacy Protections: The current use of shared online identifiers, such as browser cookies, enables malicious actors to more easily obtain our personal information. Identity systems that rely on personal information such as email addresses, phone numbers and even Social Security Numbers are similarly easy to compromise. Furthermore, businesses often lack the resources or motivation to adequately safeguard your personal information.
- Centralized Discovery: Online identities need to be discoverable in order to be useful, in the sense that an entity you’re trying to interact with needs a way of looking up who you claim to be. Traditionally this has resulted in the use of centralized identity directories, which can often be cross-referenced and result in the over-sharing of private identifying information.
Even if you use a password manager for convenience or spend most of your time on multi-service platforms such as Google (which allow you to access multiple services with a single click), you are still delegating control of your online personas to third-party authenticators. The alternative is to personally decide with whom, and how, you choose to share specific aspects of your online persona.
This lack of personal control over our online identities and personal data has given rise to the philosophy of self-sovereign identity (SSI). In essence, a person who has an SSI has sole ownership of their digital and analog identities, as well as control over how their personal data is used or shared. Below we cover the primary components of a self-sovereign identity, and the potential ramifications of this radical new approach to digital identity management.
What Are the Characteristics of a Self-Sovereign Identity?
While the concept of SSI has existed in the abstract for decades, it wasn’t until the advent of blockchain that this theoretical concept could be translated into a working application. Every SSI system must exhibit the following qualities:
- Persistence: An SSI must be fully owned by the person who creates it and be permanent and non-reusable. As a result, an SSI can’t be decommissioned or destroyed by anyone except the owner.
- Decentralization: An SSI holder is in control of the relationships they form and the information they share, and therefore relies on a peer-to-peer network rather than a traditional client-server network architecture.
- Privacy Protections: SSI owners control how their information is shared and used, and therefore every request to use an SSI owner’s personal information requires explicit consent from the owner.
- Portability: An SSI must be interoperable and device- and network-agnostic in order to achieve true self-sovereignty.
How Do Self-Sovereign Identities Work?
There are many approaches to establishing a decentralized ecosystem of self-sovereign identities. They can generally be distilled into a general framework comprised of the following components:
- Decentralized Identifiers (DIDs): A DID is a cryptographically secure and machine-verifiable string of values which can uniquely identify a person without relying on a centralized authority. DIDs use public and private key pairs to secure information and handle permissions, and are designed to work across different blockchains, software libraries, and protocols. Every DID has the following two components:
- DID Document: A DID document contains cryptographic materials which describe the DID holder and enable the DID holder to prove control of the DID.
- DID Method: A DID method is the mechanism used to create, read, update, and deactivate a DID and its associated DID Document on a specific distributed network.
Simply put, a DID is decentralized proof of who you are. And, in contrast to IP addresses, which provide a way for devices to interact with one another, DIDs provide a way for individuals and other device-agnostic entities to communicate. DIDs are on track to become the first new type of online identifier approved by the World Wide Web Consortium (W3C) since the URL, and an entity can have as many DIDs as necessary, with each DID associated with a specific aspect of a person’s online identity.
- Personally Identifiable Information (PII): Your PII is composed of your private information and your online interactions. Types of private information can include government-issued identifiers, like social security numbers, your birthdate, phone number, or any other information that can be used to track someone. The online interaction component of your PII consists of an array of claims, verifiable credentials, and verifiable presentations:
- Claims: A claim is a statement about a subject which is typically expressed using a subject-property-value relationship. For example, Satoshi (subject) - Created (property) - Bitcoin (value). Multiple claims can be strung together to create a network of information incorporating multiple subjects and their relationships to other subjects or pieces of information.
- Verifiable Credentials: Verifiable credentials are a set of one or more claims made by the same person, and typically also include a unique identifier and corresponding metadata which describe the properties of the credential.
- Verifiable Presentations: A verifiable presentation is one or more sets of verifiable credentials which collectively constitute a subset of a person’s PII. For example, when asked to prove your nationality you will be able to ‘present’ proof of your country of origin without revealing your birthdate or full name, unlike when you show your passport to a customs agent. Verifiable presentations are key to SSI since they enable individuals to only express the specific aspects of their online persona they chose to divulge.
As a result, within the context of the SSI framework, your PPI can be interpreted as either “who you are” or “a specific action you claim responsibility for,” depending on the specific context in which it is applied.
The underlying cryptographic process enabling the SSI components to interact can be generalized as such:
- An SSI solution uses a distributed ledger to establish immutable records of specific events, initiated by or involving a unique DID, in the form of a verifiable credential and/or verifiable presentation.
- The verifiable credential/presentation is cryptographically shared between network peers within a decentralized network, or between separate but connected decentralized networks.
- The recipient of a verifiable credential/presentation then uses the DID associated with that credential/presentation as a discovery mechanism to send a person’s public verification key. It can then be used to decode and validate the data within the verifiable credential/presentation and complete the interaction.
It’s important to note that under an SSI system an entity’s verifiable credentials/presentations are not themselves stored on a blockchain ledger. Rather, blockchain technology is used as a transparent, immutable, and secure method to exchange cryptographic keys linked to an entity’s immutable identifying information.
Truly Own Your Online Identity
When the internet was initially developed in the 1960s, it was designed to connect devices together in order to share information and resources across multiple networks. However, the internet’s IP protocol is only capable of determining the addresses of the devices you are connecting to and cannot verify the identity of the entity controlling the device.
Self-sovereign identity gives us an autonomous and definitive method of proving who we are and who we are interacting with.
While the precise methodologies for creating an SSI are still in development and have yet to be standardized, the goal is clear: the establishment of a decentralized, interoperable system of online identity management which serves as a codified representation of online user autonomy and individual self-determination. Therefore, SSI embodies the future of digital identity management and is one of the purest expressions of blockchain technology’s latent potential.
Cryptopedia does not guarantee the reliability of the Site content and shall not be held liable for any errors, omissions, or inaccuracies. The opinions and views expressed in any Cryptopedia article are solely those of the author(s) and do not reflect the opinions of Gemini or its management. The information provided on the Site is for informational purposes only, and it does not constitute an endorsement of any of the products and services discussed or investment, financial, or trading advice. A qualified professional should be consulted prior to making financial decisions. Please visit our Cryptopedia Site Policy to learn more.
What Is a Self-Sovereign Identity?
Personal control over our online personas has given rise to the philosophy of self-sovereign identity (SSI). In essence, a person who has an SSI has sole ownership of their digital and analog identities and controls how their data is viewed or shared.

Gemini Cryptopedia
Gemini is a next generation cryptocurrency exchange and custodian that allows customers to buy, sell, and store digital assets.
Vault12 is NOT a financial institution, cryptocurrency exchange, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys for the purpose of inheritance. We provide no legal or financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
You will lose your Bitcoin and other crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
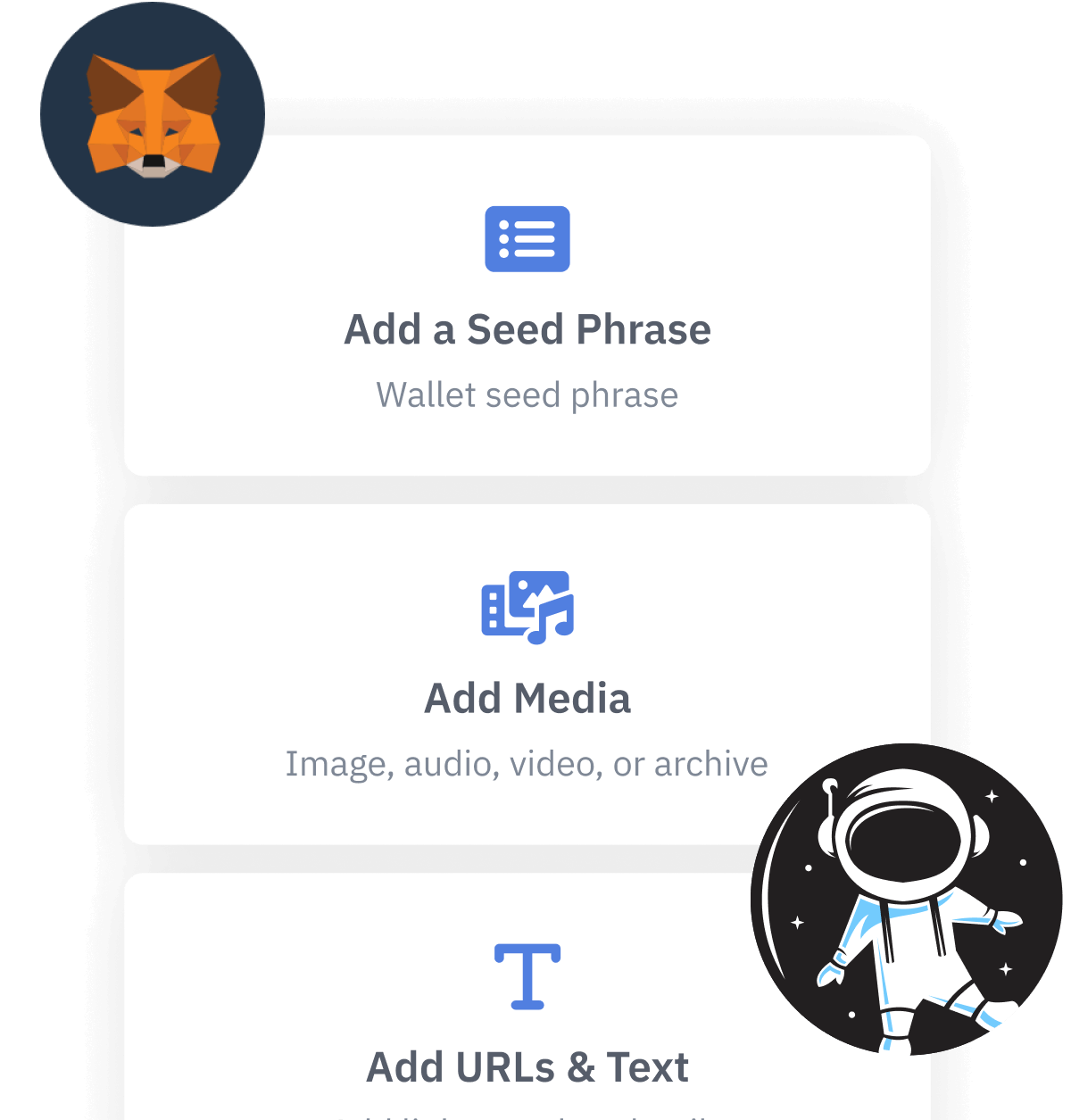
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
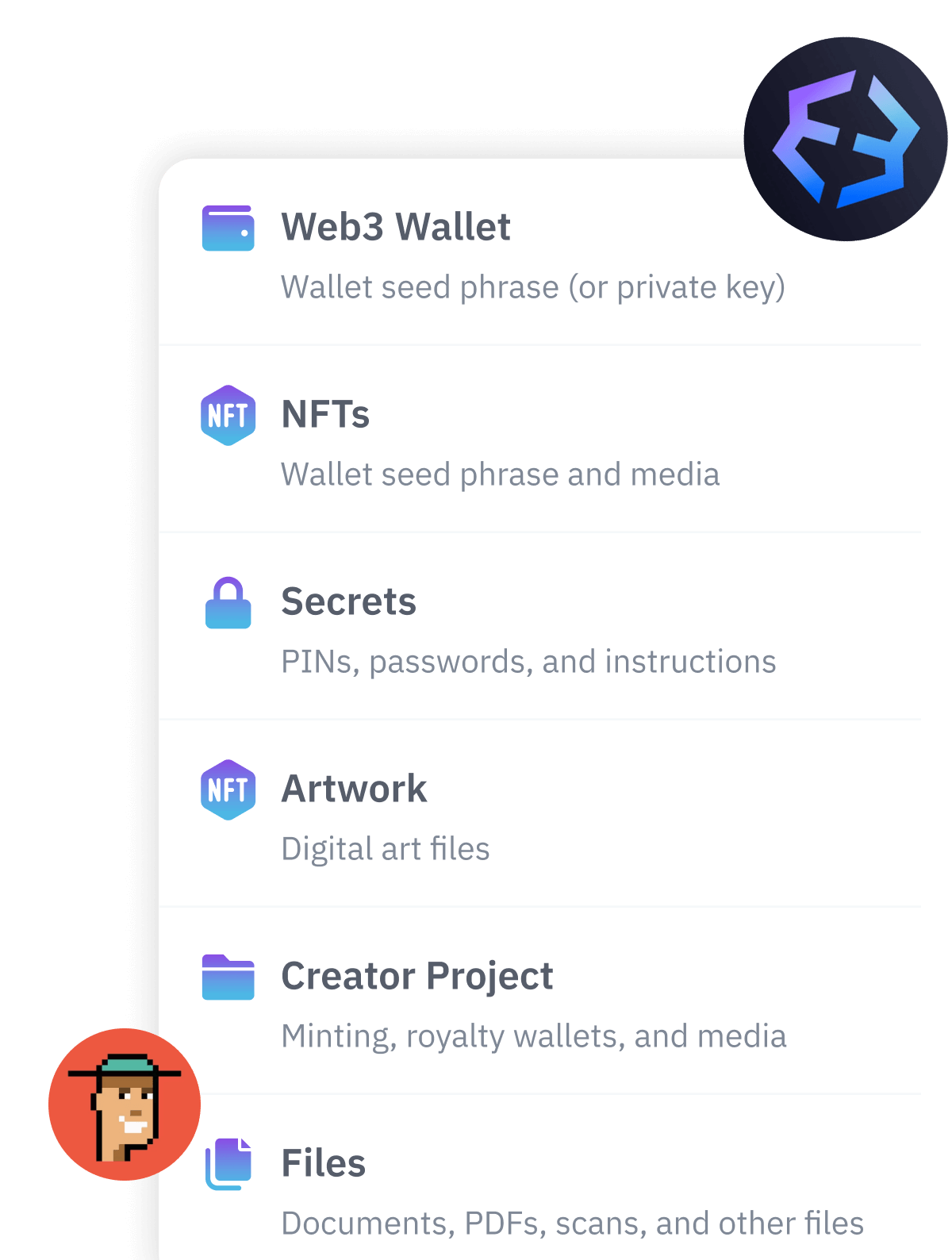
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.