Contents
- Key Highlights: How do you keep crypto passwords safe?
- Do you have a lot of passwords to manage?
- How should you store your crypto passwords, passphrases, PINs, keys, and secrets?
- Passwords are a security protection that we love to hate
- Why should you never re-use passwords?
- Why do passwords have to be so complicated?
- What is a rememberable passphrase versus a complex password?
- How do you choose strong passphrases?
- Does Multi-Factor Authentication add security to passwords?
- Should you have multiple password managers to avoid a Single Point of Failure?
- Should you choose a locally-installed or online password manager?
- Should you use an open-source or commercial password manager?
- Do some password managers have vulnerabilities?
- How can you choose the right password manager for you?
- Where can you find Password Manager links and reviews?
- Back up your password manager's master password securely to Vault12
What you need to know about password managers for crypto
Password manager software helps you to securely choose, store, and maintain your passwords and secrets.
Cyber threats and scams targeting crypto assets are increasingly common and sophisticated, so the importance of securing your digital assets is more critical now than ever. You may have wondered whether password manager software could help you to reduce your crypto security risks. In this guide, we'll cover the basics of passwords and their management, and consider some ways that you could manage your cryptocurrency passwords.
Key Highlights: How do you keep crypto passwords safe?
Keep the following in mind when developing your strategy for managing passwords for cryptocurrency:
- It's not easy: Managing passwords is challenging!
- Security is more important than convenience: Passwords must be kept secure from prying eyes (but also be readily available to you).
- Password length is key: Carefully-chosen multi-word passphrases can yield long passwords that can be both secure and rememberable.
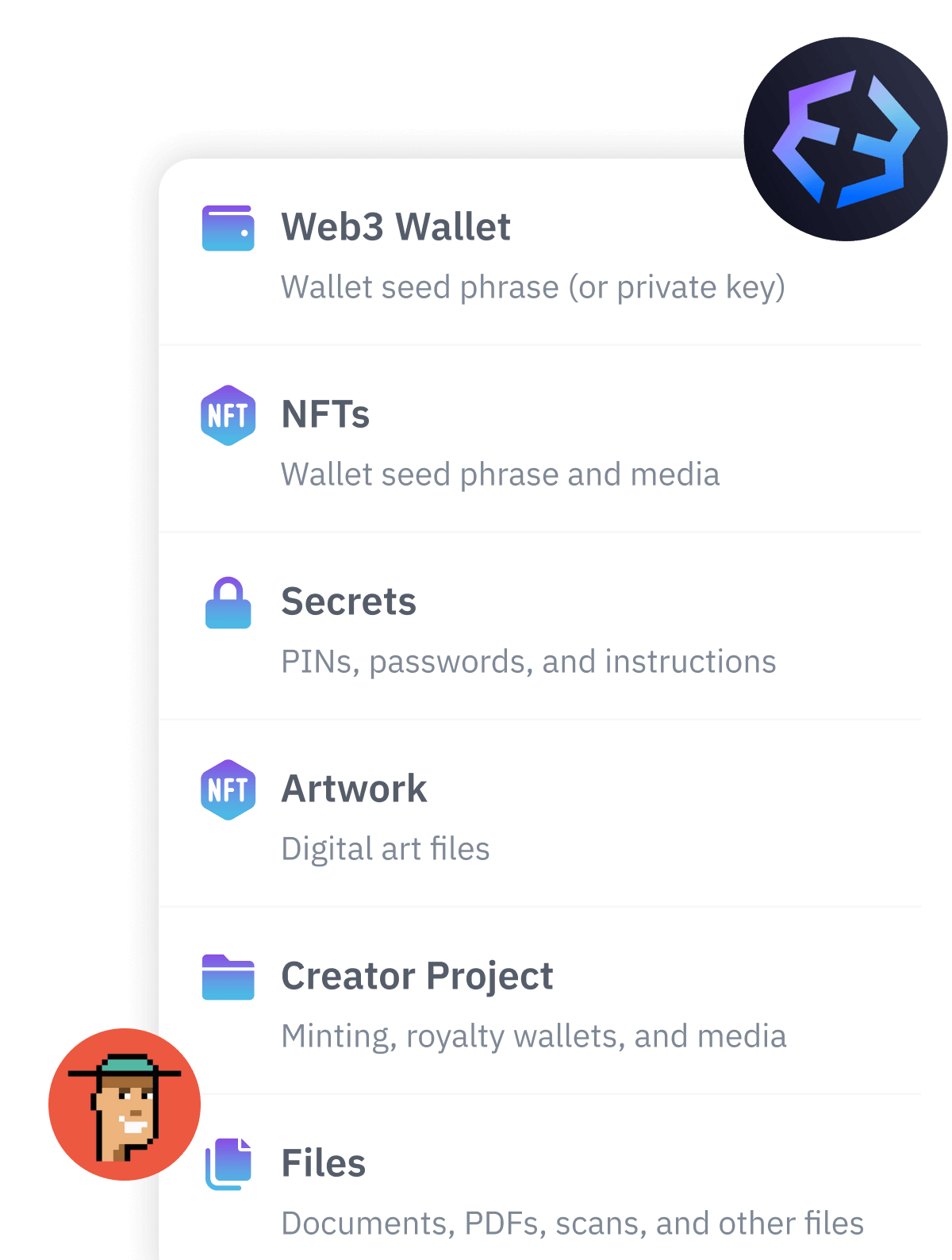
- Password managers can help: "Secrets" to be stored in password managers may include passwords, PINs, encryption keys, answers to "secret questions," and other sensitive data.
- You have lots of options: There are many password manager tools available, and each has tradeoffs. Consider strategies to avoid "putting all your eggs in one basket."
Do you have a lot of passwords to manage?
Do you feel overwhelmed by the number of passwords that you have to use? There are passwords for the computer systems that you keep at your home: laptops, mobile phones, wifi passwords, router passwords, and so on. Beyond those, we manage many of life's tasks using online accounts:
- cloud or iCloud-based services
- bank, investment, and retirement accounts
- insurance
- taxes
- doctors and medical insurance
- travel services
- property registration
- pet services
- entertainment
- social media
- shopping clubs
- grocery deliveries, etc.
It is hard to think of anything we do that doesn't have an online "footprint!" But along with this explosion of online accounts, security experts warn "Don't re-use your password for multiple accounts," and "Make sure your passwords are long and hard to guess." Further, experts recommend changing your passwords regularly even when they are unique and strong. But realistically, how are we supposed to choose, store, and maintain tens if not hundreds of unique passwords?
How should you store your crypto passwords, passphrases, PINs, keys, and secrets?
There are many choices in how we buy and store cryptocurrency and digital assets, and crypto-related accounts are responsible for just a subset of our entire fleet of passwords. Whether you use hot wallets, cold wallets, web-based exchanges, 2FA token generators, cloud accounts, and/or other mechanisms, you have accumulated at least a handful of passwords and other secrets along the way. You probably have all of the below:
- Crypto exchange passwords (and 2FA recovery codes)
- Software and hardware wallet passwords, PINs (and more 2FA recovery codes)
- Wallet Private keys, perhaps in the form of BIP39 seed phrases and additional passphrases
- Passwords for email accounts used for crypto activity (transactions, confirmations, or recovery)
Some of these include:
- Should you store your crypto-related passwords separately from your other passwords?
- What is the entire set of passwords that a trusted beneficiary would need to know in order to access your crypto accounts?
- Are your crypto-related passwords strong enough? Should they be longer or more complex?
- How can you be sure that your crypto-related passwords have not been previously involved in a data breach?
- How should you choose the right password manager for you?
Passwords are a security protection that we love to hate
No matter how you choose and maintain your account passwords, it is a chore to use them. Not only are there too many passwords for you realistically to remember, it is complicated and error-prone to type them in. Why are passwords so inconvenient? The answer is because it is hard to stay a step ahead of hackers, who are always looking for ways to break into our accounts.
Adding to these challenges, many web sites have a frustrating tendency to automatically log you out after a few minutes of inactivity, forcing you to log in again. (This is a security protection: it makes it less likely that bad actors could gain access to your account by stealing your active user account session.) To make it easier to log in again, some web browsers offer to "remember" web site passwords for you, but that is not the safest way to store them, and many high-security web sites block browsers from offering you this convenience.
To make your life easier, you may be tempted to take shortcuts: some people resort to choosing the shortest and most easily-remembered passwords they can get away with. Some people reuse the same password for many sites. Some people rely on the "forgot my password" function every time they log in, rather than have to keep track of passwords. Such shortcuts are not a good idea for high-value accounts.
Why should you never re-use passwords?
When web sites are hacked, hackers steal a treasure trove of information, which unfortunately sometimes includes usernames and passwords ("credentials"). This information is then often sold on the black market, or just released to the public, depending on whether the hacker is motivated by financial gain, fame, or simple mayhem. As soon as these stolen credentials are released, hackers worldwide immediately start trying to log in to many other web sites with the same or slightly-modified credentials - they use tools to do this with amazing efficiency. For this reason, if you re-use the same username and password for multiple web sites, it is only a matter of time until your accounts are hacked by one of these credential-stuffing attacks.
One of the most helpful resources to help you see whether a specific email address, phone number, or password has been involved in a data breach is to check the web site https://haveibeenpwned.com, which was developed by security expert Troy Hunt. Quite a few password manager tools integrate with this web site to make sure that your chosen passwords are not recognized as having been involved in a previous data breach (in which case, they will warn you).
Password managers support you by suggesting secure passwords that avoid password reuse, and they encourage you to regularly change your passwords. In these ways, password managers lead you to practice good "digital hygiene."
Why do passwords have to be so complicated?
If hackers don't have a nice convenient list of hacked passwords, they will simply try to guess them - and they are extremely good at guessing. For example, if they know that a certain web site requires passwords that are at least 8 characters long and with at least one special character, they will be sure to guess only valid passwords that meet those criteria. If they know that a web site will lock user accounts out after a certain number of failed login attempts in a certain amount of time, they will program their attempts to avoid that lockout - to "fly under the radar." If they know that your username was associated with a given password on one hacked site, they will try using your username with variations of that password on different sites. If they know things about your life from your social media accounts, like the names of your children or pets, they will try to incorporate those clues into your passwords. Do your best to set truly "unguessable" passwords.
Long, complex, and unique passwords are not very vulnerable to hackers because they are not easily guessable.
What is a rememberable passphrase versus a complex password?
There is an alternative way to create an extremely hard-to-guess password instead of relying on a long, complex string of random characters. Many experts agree that great passwords can be formed from a series of regular words that you can actually remember: a multi-word passphrase. Some people call these long, multi-word passwords "pass sentences," but in this article, we will use the more common and general term "passphrase."
To avoid confusion: You may remember that your BIP-39-compatible crypto wallet has something called a passphrase, too. A passphrase is a specific term for a string that is used as an additional authentication mechanism in cryptocurrency wallets. The passphrase could be a password or a multi-word passphrase, but it is a specific case of passphrase use, and in this article, we are discussing passphrases in a more general sense.
What makes a password or passphrase hard to guess is how long and unpredictable it is. Longer passwords are less-guessable than short passwords because there are more possible combinations of characters - even if they take the form of a series of words with no character complexity. With passphrases, by the way, it is recommended to leave spaces between words, if the system accepts space characters.
However, often you will not be allowed to use a word-based passphrase instead of a complex password ... the system that you are accessing makes the rules for what kind of password or passphrase it will accept, and it may demand upper-case, lower-case, and special characters. But you
could come up with a long passphrase that happens to have enough complex characters that it would be both rememberable and complex enough for the underlying system ... something like "Hammerhead&species&make&quirky&silhouettes." It is still admittedly awkward ... but maybe easier to remember?
Here are some points to consider about the tradeoffs involved:
- The passwords or passphrases that you use to access your password manager(s) are good candidates to be both strong and rememberable - for example, you may first need to log into your primary laptop or workstation (which may have both a full-disk encryption unlock password and an operating system login password), and then you likely need to provide another password or passphrase to access your password manager application.
- If you access a system every day, it becomes easier for you to remember that password. But if you only occasionally access a system, no matter how rememberable the password is, you will probably still forget it. Be very careful relying on your memory for password storage!
- Even though it may be easier for you to remember a passphrase of 4 or more words than a string of random characters, it may not be practical for you to remember either, especially when you have multiple passphrases to remember. So consider: what is the smallest number of passwords that you would need to access a password manager that could hold the rest of your passwords - and could at least those passwords be long and rememberable?
- When deciding whether to rely on your memory for a given password or passphrase, be sure that you have considered how large the consequences would be if you forgot it, or if you became unavailable.
- Despite popular belief, it is not always a terrible thing to write down your password or passphrase on a physical medium like paper - as long as that medium is kept safe from loss, theft, and threats - for example in a fireproof safe!
- A conspicuous solution: the Vault12 Digital Vault is an excellent mechanism that can be used to securely back up your most-critical master passwords.
How do you choose strong passphrases?
Most password managers offer users the ability to generate strong, complex passwords made up of randomized characters, and this greatly streamlines the process of coming up with them yourself. But what if you would like to try to create strong passphrases, instead of or in addition to passwords?
An important characteristic of strong passphrases is that the more randomized the words are, the stronger the passphrase. A conventional passphrase that you simply make up from common words (e.g., "I like to eat bacon and eggs") may be quite guessable despite its 7 words and 29-character length. There is a famous cartoon strip from xkcd that popularized the set of words "correct horse battery staple" as a secure and easy-to-remember passphrase. This passphrase has become popularized to the degree that it often is used as a starting point in analyses of the concept of passphrase security in vendor guidance and academic studies.
If you would like to further explore how to create secure passphrases, there is a word dictionary and more-detailed advice about how to create a strong passphrase using dice at the Electronic Frontier Foundation (EFF).
Does Multi-Factor Authentication add security to passwords?
With all of these password-guessing risks, why are passwords still used to authenticate us to our accounts? Even with their limitations, passwords are simple to implement, and — if they are well-chosen — they can be very strong. But because of the inherent risks of various forms of password-hacking, password protection by itself is not sufficient for high-security accounts. This is why 2-factor Authentication (2FA) or multi-factor Authentication (MFA) frequently is used along with passwords or passphrases to achieve higher security for important accounts. If you want to know more, here is another article offering practical details about 2FA.
Ultimately, multi-factor authentication is more than just a convenience feature for a password manager — it is a core function. 2FA or MFA should be required when you log in to the application, and also when you reset your password (password recovery). When you choose and set up your password manager, ensure that it offers you the ability to use authentication mechanisms that are secure. Password managers vary in the authentication options that they offer, and they do not force users to choose only the most-secure options. Ensure that you choose the strongest multi-factor options that you can for your password manager — do not, for example, rely solely on confirming an SMS message to reset your password manager password! See the Vault12 article about 2FA if you need more details about these risks and how to make strong choices for 2FA. Consider incorporating biometric authentication as one of your factors if possible.
Should you have multiple password managers to avoid a Single Point of Failure?
But is it sensible to keep all of your passwords and secrets in one place? It is logical to worry about "keeping all of your eggs in one basket," or having a single point of failure. On the other hand, who wants to individually set up and protect many different baskets? As you consider how to organize your passwords in a password manager, you may want to consider keeping two or even more password managers. There is no single best organizational strategy for how many password managers to keep, and as you might expect, there are several factors to consider:
- It is generally safe to use password managers, but they are a juicy target. The more frequently you use a given password manager, the greater the chance that someone will somehow learn that you use it, and it could become more of a target for hacking. There is always a greater risk of exploitation of any software that is installed on a frequently-used, sloppily-patched, internet-connected computer relative to software kept on a limited-use, carefully-protected computer. You want to protect your password manager - so don't keep a password manager with your important secrets installed on the same machine that you let your kids use for playing games and general browsing.
- Many experts recommend that you keep all crypto-related account information and secrets separate from those that you use for your "regular" personal tasks. This advice may lead you to maintain a dedicated password manager for just your crypto-related secrets, and one password manager for "everything else," especially if you have a sizable investment in cryptocurrency.
- Also, it would reduce risk to store your 2FA recovery codes separately from your passwords. Plenty of people keep them together - but effectively, keeping them together turns two-factor authentication back into single-factor authentication, since if your password manager were ever hacked, the combined set would become just one "something that you know" factor — and the hacker would discover both.
Should you choose a locally-installed or online password manager?
Many password managers are kept online, in Cloud services, but some password managers can be kept on a local computer. If your password manager can be stored locally, it can be available to you for offline use, which may be handy. Which is more secure - online or offline? It depends on how good you are at keeping your own computers secure and backed up. Cloud providers have professionally-configured, regularly-patched machines, with constantly-monitored security protections - can you match that level of care? On the other hand, if you know how to secure and maintain a limited-exposure home computer, and you maintain regular, secure backups to recover from in case of disk failure, you could safely keep a secure password manager on just your local machines. Many people walk a middle path by using a locally-installed password manager that backs itself up (in encrypted form) to the Cloud.
Should you use an open-source or commercial password manager?
Open-source software was once a niche choice, but today, even the largest organizations use free and open-source software. At the same time, there are plenty of commercial software development companies that produce software that is sold for a licensing fee. Which is better for a password manager?
Let's consider the general advantages and disadvantages:
- Open-source software offers complete code transparency - any programmer in the world can review the code, and submit bug reports and security concerns. For projects that have many people involved, this process yields extremely high-quality, high-security code.
- However, some open-source software projects lose participatory momentum over time, lose "eyeballs" and users, and as a result, become less secure. There is no institutional body that labels open source projects as "active" or "inactive," although there are signs of activity if you understand what to look for (such as activity levels of the code repository).
- Open-source software generally does not offer technical support outside of FAQs and blog-like forums. However, commercial companies often offer little more support than that. If you purchase technical support from a commercial company, there is at least some committed level of customized help and response time.
- Usually commercial software has integrations that work smoothly with other software that the same company produces — so if you are using other software products from the same vendor, and it integrates with their password manager, it might make sense to go with that company for the full suite.
Do some password managers have vulnerabilities?
No software is immune from code vulnerabilities. Both open source and commercial password managers have had vulnerabilities, and just like any other software, after they come to light, there is a flurry of activity to fix them and to inform users and the rest of the industry about what happened. Just because you may have used one of the password managers mentioned below does not necessarily mean that your passwords could have been stolen — some of these vulnerabilities were identified and fixed before they were known to be exploited, and some would have affected only users who were lured into falling for phishing attacks, or who had other malware installed already.
Some past vulnerabilities that have affected 1Password, LastPass, and KeePass are described here. And one that affected Kaspersky is described here.
You should ensure that your password manager (as well as your other software) is configured to frequently check for and apply security updates.
How can you choose the right password manager for you?
Your choice of password manager will largely depend on which features you want, and how much you want to spend. Many free versions limit cross-device synching, number of passwords stored, and other features. Also consider the reputation of the organization that produces and maintains the software.
Below are some of the features that vary between password managers, and some comparative reviews of the most popular ones.
Common password manager features
- cross-platform support (with cross-device syncing)
- online versus local password storage / offline availability
- web form-filling
- password and/or passphrase creation
- detect weak or duplicate passwords
- 2FA authentication options
There is also an advanced feature called "plausible deniability" that several password managers are in the process of considering for implementation. With plausible deniability, a user can set up one password that appears to give access to the entire set of stored passwords, but actually only allows access to a subset of less-important passwords. The user can also configure a second password, which if used instead, would reveal the more high-value passwords. Plausible deniability is already implemented by some crypto hardware wallets, but as a tricky and advanced feature, it is not yet common in popular software-based password managers.
Where can you find Password Manager links and reviews?
Below is a list of direct links to popular password managers:
- KeePass (free)
- iCloud Keychain (Apple only)
- 1Password (commercial)
- Keeper (commercial)
- LastPass (free and commercial versions)
- BitWarden (free and commercial versions)
And here are some recent comparative reviews that can help you choose from among them:
- PC Magazine (comparison of free password managers)
- CNET
Back up your password manager's master password securely to Vault12
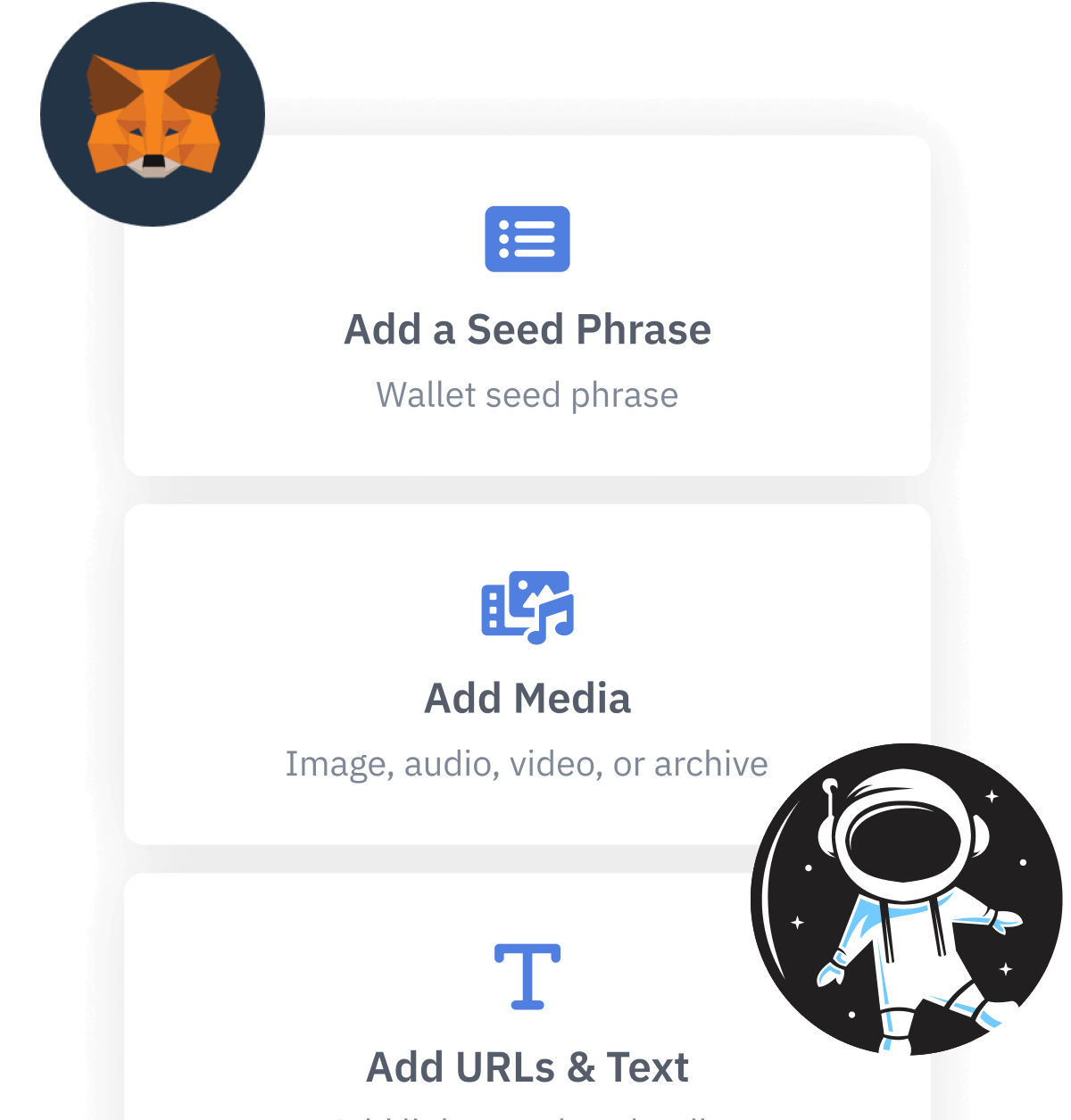
To make your password management easier and more secure, we suggest that you use your Vault12 Digital Vault to store your password manager's master password, and any other passwords needed to access your password manager. Safely in your Digital Vault, they act as fallback protection in case, despite your best efforts, you forget them. Your Vault12 Digital Vault is not a full-featured password manager, but it is a perfect repository where you can safely keep your "master" passwords that guard access to your password manager. Just remember to update them in your Digital Vault when you change them.
What you need to know about password managers for crypto
Password manager software helps you to securely choose, store, and maintain your passwords and secrets.

Art Krotou
Art is a crypto-security expert and researcher with serial entrepreneurship background. Having a degree in physics and experiences in multiple cutting-edge industries like fintech, secure hardware and semiconductors, and identity gave him a unique multi-faceted perspective on the problem of key management for individuals in the crypto networks and the evolution of the internet in general.
In his current work, he is specifically researching how cryptographic keys can be inherited without posing a threat to 3rd parties in edge cases. In addition, he advocates for "fault-tolerance via secrets automation". He discusses the quantitative impact of user experience factors on the uptake of non-custodial solutions.
As one of his most notable accomplishments, he co-founded and led through the early years of the company that contributed to the complex technology behind Apple's recent M-series CPUs. He is also the creator of the most friendly and aesthetically pleasing, but nonetheless super secure and fault-tolerant hardware wallet - U•HODL.
Check out his curated series of "Vault12 Learn" contributions below, and follow him on Twitter and LinkedIn for more sharp insights.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
You will lose your Bitcoin and other crypto when you die...
...unless you set up Crypto Inheritance Management today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate onspecific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Crypto Inheritance Management: Secure, Self-Custody Crypto Inheritance and Backup
Vault12 is the pioneer in Crypto Inheritance Management, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.