Contents
- Cloud + encryption = best of all worlds?
- High-level view of Cloud storage advantages and disadvantages.
- Risks of lost access.
- Human error in using your Cloud account.
- General risks for handling seed phrases on computers.
- Risks during and after encryption.
- Encrypting before putting secrets into the Cloud.
- File-level encryption.
- File encryption tool choices.
- MacOS disk image encryption.
- Cloud-based password managers.
- The simplest way.
How to use Cloud storage to back up your Seed Phrase.
Read this article if you want to better understand the strengths and potential pitfalls in storing your seed phrase in the Cloud.
One of the many ways that you could choose to back up your crytocurrency seed phrase would be to back it up to the Cloud. Although Cloud storage is not risk-free, proper encryption of your seed phrase before storing it there lowers the risk and makes it an option that you might consider.
TL;DR (concentrated takeaways)
If you rely on Cloud storage for backing up your seed phrase, you must encrypt it first - else it is extremely poorly protected. Cloud storage is a target!
It is critical that any computer that you use for encryption, or for viewing your seed phrase, be free from malware.
Although Cloud storage is convenient and robust, it has risks largely due to its complexity and by how much potential access could accidentally or maliciously be granted to data stored there.
There is a potentially overwhelming array of options and tools available to perform encryption.
Password managers can be effective and convenient for some secrets, but their operation must also be well-understood in order to provide the safety that they are meant to provide.
For anything that you encrypt, you must keep and store a backup of the decryption key (too)!
Cloud + encryption = best of all worlds?
On the surface, the peace of mind that Cloud providers offer by taking responsibility for long-term digital file storage seems to make the Cloud the perfect place to store your seed phrase! However, news reports cover with alarming frequency tales about information being stolen from various Cloud storage repositories, whether due to inappropriate permission configuration, software vulnerabilities, or even insider theft by employees with authorized access to computer systems, networks, or recycled hardware. Cloud security can be excellent, but it is not perfect - especially the parts that rely on human diligence. This is why it is important for your sensitive information stored in the Cloud to be encrypted before being placed there. If someone were to gain illegitimate access to your Cloud files, but those files were strongly encrypted, the would-be thieves could not read the contents.
So ... Cloud storage is great but has risks ... encryption offers some protection ... let's think about how we could put these two technologies together into a strategy that offers a high level of security with minimal risks.
High-level view of Cloud storage advantages and disadvantages.
Advantages of backing up an encrypted form of your seed phrase to Cloud:
- Convenience
- Reduced risk of physical loss or media failure
- Reduced risk from natural disasters
- Good security controls when carefully applied
Disadvantages of backing up an encrypted form of your seed phrase to Cloud:
- Complexity - more pieces to the puzzle
- More copies - the Cloud provider too will make backups
- Wider access - role-based permissions for controlled public access, and Cloud staff access
- Risk of lost access to the Cloud account
- Accidental deletion
- Accidental disclosure
- Error in encrypting
- Possibility of being hacked
Cloud account hacks and takeovers happen regularly. You must take precautions in protecting your Cloud account and be wary of attempted hacks.
Risks of lost access.
Even though it seems inconceivable that large Cloud providers could go out of business, corporate hiccups like downtime, legal holds or threats, and other unpredictable disruptions are possible.
It is also rare but possible that you could lose access to your Cloud account by forgetting information needed to authenticate yourself, or through a long period of disuse. It can also be challenging for next of kin to gain access to your Cloud accounts.
To protect yourself against corporate crises, the only thing you can really do is to try to stick with large, reputable companies that have high protection against all kinds of disruptions: Google, Apple, Microsoft ... these companies are well-positioned for stability, and have an excellent reputation for reliability.
To protect yourself from loss of access, make sure that you keep your Cloud profile information updated with correct contact information ... for example, if the phone number that you receive 2-factor confirmations on changes, update it! If your name or address changes, let them know! Any information that you use to authenticate to your account should be kept up to date.
Also, don't create a new account to store your seed phrase with an intent to "set it and forget it." Sometimes long-term inactivity can lead a company to disable or de-activate an account. Remind them that you are still a valid user by logging into it at least occasionally.
Human error in using your Cloud account.
Storing information in the Cloud is handy due to its convenience and reliability. In fact, a growing number of people are getting into the habit of uploading all of their valued files there, including a wide assortment of sensitive and non-sensitive information, from tax statements to vacation pictures to phone and laptop backups. But consider that people have highly-varying organizational skills for how well they group and label their files, and they have different levels of carefulness and awareness when granting permission for others to access them. Many applications now offer the ability to "Share" Cloud files in an integrated way - it is not always intuitive or clear when you are granting people permission to access certain of your Cloud files. Your ability to use Cloud storage to keep sensitive information secure depends on your technical skills - It can be challenging to keep a large and growing set of Cloud files organized and with the right permissions assigned.
It is these human errors that could lead to your accidentally disclosing a Cloud-stored seed phrase to another party by mistake, or deleting it during a "cleanup," or accidentally uploading a version of it that is not encrypted as you thought it was. We all make mistakes, and we make more mistakes when things are complicated, when we are multi-tasking, or when we are in a rush.
General risks for handling seed phrases on computers.
Let's review the risks of backing up your seed phrase to any computer media, and then explore some of the unique risks that affect Cloud-based backup methods specifically.
A general security risk for all computer-based backups is that any computer used to type, store, or display the seed phrase in unencrypted form could have been compromised with malware. Computers that have been compromised with malware can "observe" anything that is communicated through the keyboard or screen, and in some cases, also what is processed in memory, so you want to be as sure as you can be that you use a computer that has not been compromised. Because it is so hard to be confident in an average computer system's security, many people use temporary ("live") operating systems like Tails Linux when working with unencrypted cryptocurrency seed phrases.
A second general risk for computer-based backups is the fact that all computer media will eventually fail. The only way to accomplish long-term storage on a computer is to have a careful plan for rotating and securing your backups on a regular schedule that would allow recovery if any individual form of media were to fail. Companies that have to back up important information on computers have entire teams dedicated to figuring out how to accomplish this, and it is complicated even for these groups of dedicated professionals. Part of the beauty of Cloud storage with reputable, established companies is that there are such teams of paid professionals who have put the time into figuring out how to control the risk of media failure.
Risks during and after encryption.
Encrypting a seed phrase before storing it on a Cloud drive protects it from many threats. However, encryption itself adds some risks:
- If the computer on which an encryption tool is run has been compromised with malware, the phrase can be stolen before it is even encrypted. If this is the case, you would never know, until your funds were suddenly missing, and even then, you wouldn't know what had happened. The most effective malware is like a professional thief breaking into your house - it is silent, and leaves no traces of its activity.
- In order to decrypt the encrypted file containing the seed phrase at a later time, you need to retain the decryption key, which meanwhile needs to be stored separately. Having to securely store a decryption key increases the overall complexity of the backup, and adds an ongoing risk of loss or theft of that decryption key. Loss of the decryption key is one of the most common encryption disasters that people have, and that risk should not be underestimated!
Encrypting before putting secrets into the Cloud.
Storing a seed phrase on a Cloud drive without encryption carries similar risks to storing it locally without encryption - an unencrypted seed phrase is a sitting duck, and the risk of its discovery and theft is high. Let's take a look at some of the ways that you could avoid that risk by performing encryption before storing your seed phrase in the Cloud. Again, none of them are perfect: the methodology and risks vary for each approach.
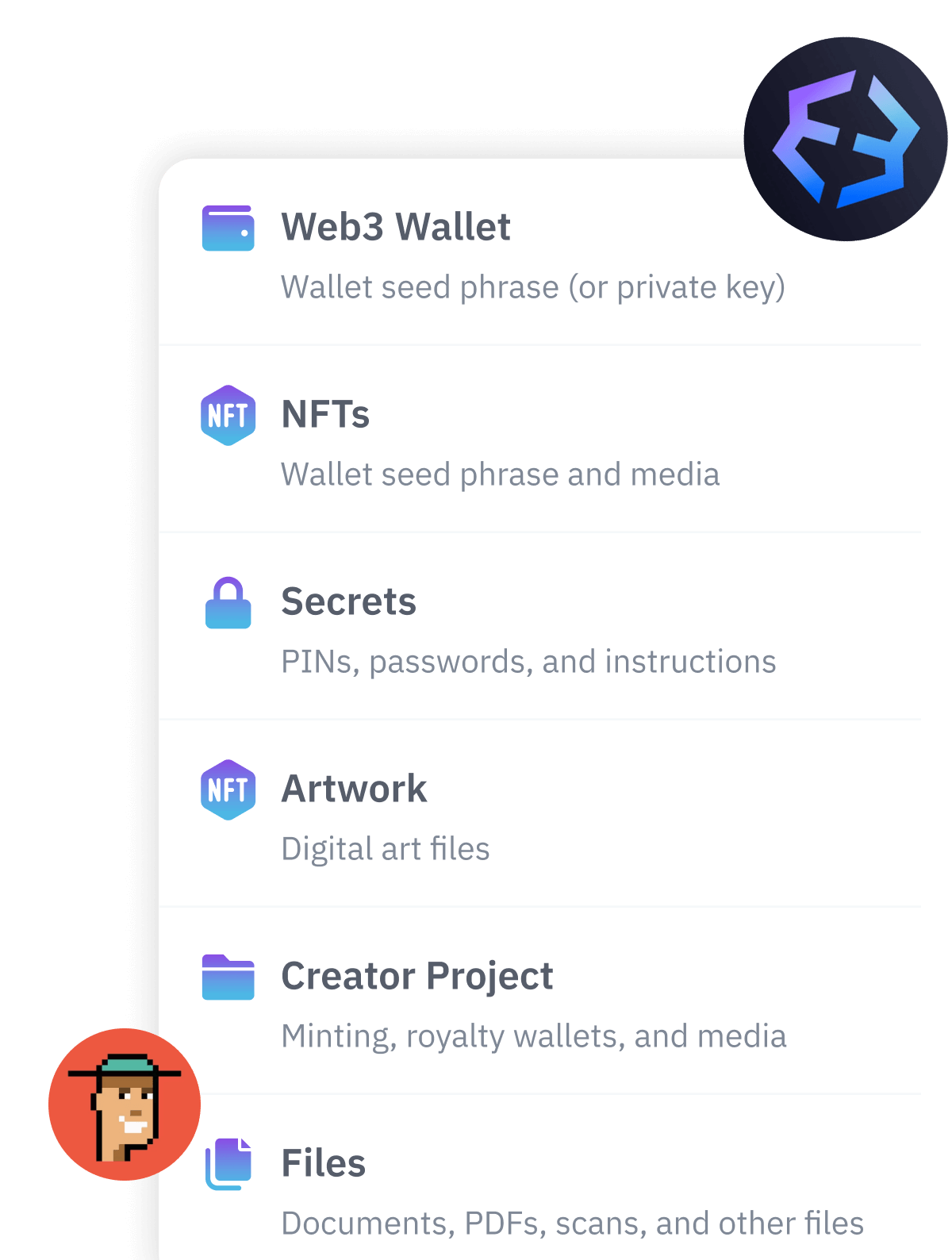
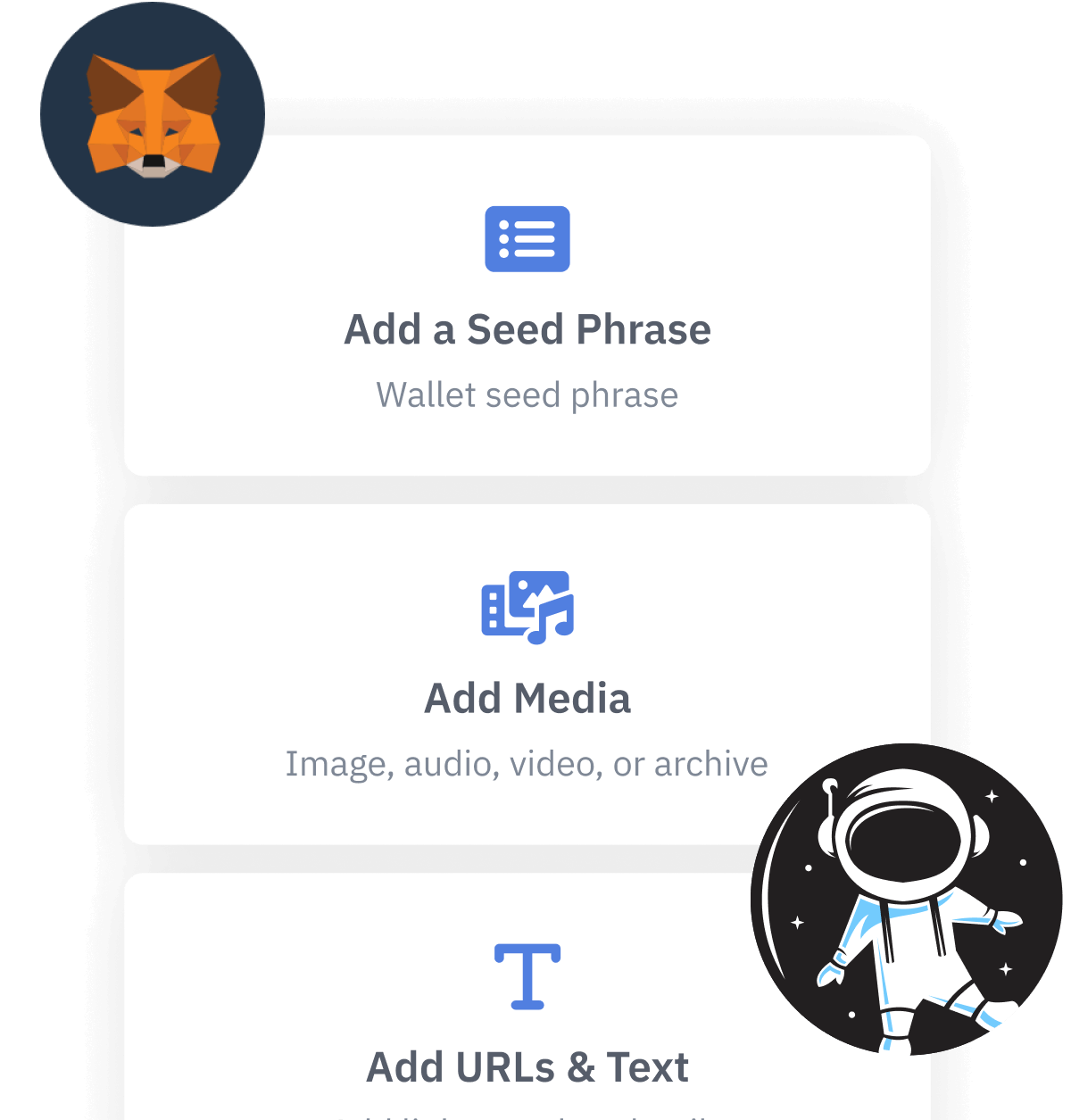
- Use a desktop encryption utility to perform file-level encryption, and then copy the file to your Cloud drive.
- Encrypt an disk drive image, and then copy the disk to your Cloud drive.
- Use a Cloud-based password manager.
File-level encryption.
You could choose to encrypt your mnemonic phrase from your laptop or desktop computer before storing it in your Cloud--based storage. To encrypt specific files, you would use file-level encryption.
There are many tools that can encrypt files. Some are user-friendly, offer many features, and integrate with other applications. Others are very simple, single-purpose tools. As with everything, opinions vary, and there is no "best" tool or single way of doing it. Some people prefer to use open-source tools, and some people prefer to use commercial tools. Most modern password managers run on multiple platforms, including MacOS, Windows, Linux, and mobile phones. Some of them can encrypt locally, and some encrypt and automatically copy files to the Cloud. It is pretty amazing how many different options there are to encrypt files.
Never use an online, web-based service where you paste in your seed phrase and they give you back an encrypted version of it. You never want your seed phrase to be sent over the internet without being encrypted first, and you never want to share it with any person or company that you do not completely trust. Companies that offer online, web-based encryption and decryption are encouraging you to be irresponsible with your data, trying to steal your information, or both.
Next, let's talk about some options for how you can encrypt files directly on your own machine.
File encryption tool choices.
Perhaps the most "classic" tool that has been used to encrypt files is "Pretty Good Privacy" (PGP). PGP was developed and released as open source software in 1991. It became legally controversial, and its creator, Phil Zimmerman, later created a version of it that became the flagship product of a company called PGP Corporation. In 2010, the company Symantec bought PGP Corporation, and folded the PGP encryption technology into the product called Symantec Encryption Desktop.
Meanwhile, the open-source implementation of PGP was still floating around, and that OpenPGP variant became an official Internet standard. Other implementations of encryption tools have been spawned from OpenPGP since, including one called GnuPrivacyGuard (GPG, aka GnuPG). Many of the encryption tools on the market today are based on OpenPGP or GPG.
To use GPG, you could check out GPG for Windows or GPG for Mac. It can be a little tricky to set up, so take it slow and be careful that you understand it as you go.
Some well-reviewed commercial tools that can perform desktop-based encryption for you are Symantec Encryption Desktop, Sensiguard, or Folder Lock. Some well-reviewed open source or free encryption tools include 7-Zip, AESCrypt, Cryptomator, or Veracrypt.
With any encryption software, follow the guidance in the user manual exactly. Start by working with sample files. Test unencrypting your files when you are done encrypting, to be sure that you understand how to encrypt and decrypt. And do not leave any unexpected unencrypted copies lying around. (For example, Windows 10 offers a "file recovery" feature that should be taken into account in order to fully eliminate transient copies of unencrypted files.) It can be surprisingly challenging to ensure that files are really deleted on your version and configuration of your computer.
Most importantly, for anything that you encrypt, be very sure not to lose your decryption password or keys!
MacOS disk image encryption.
The Apple operating system MacOS provides the ability to encrypt and back up an entire drive, rather than having to mess with file-based encryption tools.
In fact, Apple offers a variety of different ways to back up and encrypt your data, and one of the trickiest aspects to using them is figuring out which is the best way among them to encrypt your seed phrase. Some methods are intended to back up masses of data, like an encrypted Time Machine backup, or the full disk encryption utility called FileVault. But if you just want a simple, encrypted image that contains a small number of files, you can create an encrypted disk image. The exact steps will vary depending on the version of operating system you have, but often all you need to do is open Disk Utility, Choose File > New Image > Image from Folder, and point that at the folder that contains your seed phrase. Choose the encryption option that offers 256-bit encryption. Once created, you can copy that encrypted disk image to your Cloud account of choice. See Apple for details that are specific to your operating system.
Most importantly, for anything that you encrypt, be very sure not to lose your decryption password or keys!
Whether you rely on file-based or drive-based encryption, you still end up needing to save and protect a decryption password or key, which remains a single point of failure in your ability to retrieve your seed phrase.
Cloud-based password managers.
Cloud-based "password manager" applications simplify storing passwords or any strings of secret information, and they provide built-in encryption on disk. When they store passwords in the Cloud, it gives you the added benefit of being able to access them from any of your supported devices. They can also generate complex passwords better than your brain can, and their use encourages good habits like not reusing the same password in multiple places.
Risks of relying on a password manager to store a password, seed phrase, or decryption key include:
- If stored as plain-text (human readable) form in the password manager, the phrase could be stolen when it is first entered or later retrieved (if the computer used with the password manager has been compromised).
- You still need to keep track of and protect the password for the password manager.
- Like any other software, password managers are susceptible to occasional security vulnerabilities and potential exploitation. It must be maintained and kept up to date so that any discovered flaws are quickly patched.
You should choose a Cloud-based password manager that runs on all of the different operating systems that you would want to use it on.
When setting up a password manager, keep in mind that a secure password manager will always require you to perform 2-factor authentication when you log into it.
The simplest way.
From this overview of storing encrypted information in Cloud storage, you can see that although you could come up with a strategy to back up your seed phrase to the Cloud, it can be complicated, and you still have the challenge of storing your password(s) to your Cloud account and/or password manager. And you still need a way to ensure that your loved ones would know how to access the master password, and how they could can go through all of the steps to decrypt your seed phrase if you are not available to help them.
An alternative to devising your own custom, encrypted Cloud storage solution is to rely on the purposefully-designed Vault12 platform.
How to use Cloud storage to back up your Seed Phrase.
Read this article if you want to better understand the strengths and potential pitfalls in storing your seed phrase in the Cloud.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
Vault12 is NOT a financial institution, cryptocurrency exchange, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys for the purpose of inheritance. We provide no legal or financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
Prepare for the future - Don't lose your crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.