Contents
- What is a crypto wallet?
- Do I need a crypto wallet?
- What is a Custodial Wallet?
- What is a Non-Custodial Wallet?
- What Are Hot and Cold Wallets?
- Hierarchical Deterministic Wallet – HD Wallet
- What Is a Paper Wallet?
- Where do I get a wallet?
- What do I need to do to make sure my wallet is safe and secure?
What is a Crypto Wallet?
Discover the differences between wallet types, and some of the functional and security tradeoffs between them.
TL;DR (concentrated takeaways)
Your crypto wallet uses your unique encryption keys to perform your crypto trading actions on blockchain networks.
Wallets take different forms, and can be classified into types based on their design and features.
The most significant characteristic of a wallet is whether you control it, or a custodian controls it for you.
Custodian-managed wallets are not recommended for storing large quantities of cryptocurrency. "Not your keys - not your coins."
You can get a wallet from numerous sources, based on your unique needs.
What is a crypto wallet?
A crypto wallet is specialized software: a digital wallet that allows you to access your cryptocurrency. The concept of a crypto wallet is really that simple, but in practice, wallets take different forms and offer a variety of features, and there is a bit of related terminology. Here we'll help you understand the most common types.
All crypto wallets communicate information digitally, so they all perform similar functions, but they can look very different than what you usually think of when you think of a software application! Crypto wallets can take the form of user friendly, visual applications - similar to banking applications - that run on your desktop or mobile phone. If you install it on your smartphone, it's a mobile wallet. Mobile wallets excel in convenience. Other online wallets operate as a browser extension, rather than as a dedicated phone app. Yet other wallets can take the form of a small, specialized hardware device that you might not even recognize as a computer at all if you didn't know what it was.
Hardware wallets are used by security-conscious crypto owners who want their digital wallets to be highly secure, portable, and physically isolated from the Internet. They are usually only connected to your computer briefly when you want to spend some cryptocurrency. In fact, some hardware wallets can be used to transfer wallet information wirelessly, or through an exported data drive, rather than being physically connected to an internet-connected device.
Rather than storing cryptocurrency itself, a digital wallet holds private encryption keys, which the wallet uses to authorize cryptocurrency transactions, and a public encryption address, which determines where on the blockchain network your cryptocurrency is stored.
Do I need a crypto wallet?
You will need a crypto wallet if you want to transact in digital currency. All wallets perform similar functions that allow you to store and spend cryptocurrency. However, although all cryptocurrency owners need to interact with a wallet, you do not necessarily have to go to the trouble of managing your own cryptographic keys while using your wallet.
What is a Custodial Wallet?
The simplest kind of digital wallet is a custodial wallet, which you interact with through a third party (an "exchange") that helps you to buy and sell digital currencies. The way that exchanges work is similar to how your online banking application works with your bank (although exchanges do not yet offer the advantages of a bank's strict regulation). An exchange-managed wallet is considered a "custodial" type wallet because the exchange accepts the responsibility of storing the wallet, taking custody of the private keys. The user interacts with the wallet through placing requested transactions. Custodial wallets are convenient, and most are user friendly. Because they are accessible and online all the time, they might be referred to as "online wallets."
Fundamentally cryptocurrency stored in a custodial wallet physically belongs to the exchange. They simply allow you to interact with stored crypto via a web or app interface without ever truly handing over possession of the funds themselves.
There are some risks with custodial wallets: the wallet custodian could experience downtime or application sluggishness if they are overwhelmed with bursts of activity. They could be exploited by hackers, go out of business, sell their clients' marketing data, and/or be compelled by regulations to report or limit transactions. Exchanges require you to prove your identity by providing them with your personal data, and in order to allow you to buy and sell crypto with currencies like dollars, they probably need to know your bank account number, too. Additionally, most crypto held by exchanges is not insured in the way the FDIC insures bank deposits in the United States.
A corporate custodian of a digital wallet may also limit which digital currencies they allow their clients to transact with, and they may choose to restrict wallet configuration options. Because the regulatory framework around cryptocurrencies is still in its formative stages, risks associated with custodial wallets are not yet fully predictable.
In short, as commonly said in the industry, "Not your keys - not your coins." In other words, whoever holds the wallet's private keys really controls the crypto.
What is a Non-Custodial Wallet?
Users who want to manage their own wallets may choose a "non-custodial" wallet.
To get a non-custodial wallet, you would install wallet software on your desktop computer or mobile device, or purchase a hardware wallet. Non-custodial wallet owners are responsible for the security of their own wallets, including wallet seed phrase generation, securely recording and backing up their wallet seed phrase, and ensuring that unauthorized people do not have access to the wallet or the seed phrase. An example of a popular non-custodial wallet is the Exodus wallet.
We have compiled guides of a selection of the most popular crypto wallets - and will be adding more in the future.
What Are Hot and Cold Wallets?
Wallets can also be classified as "hot" versus "cold."
- Hot wallets are connected to the Internet, and always ready to be used. Hot wallets are usually software-based, and are convenient for users who regularly transact with their digital currencies. Custodial wallets on exchanges are generally hot wallets, but you could also choose to keep a self-managed wallet online all the time, thus keeping a noncustodial wallet "hot."
- Cold wallets, also known as "cold storage" wallets, are not connected to the Internet and are completely off-line, and can be either software-based or hardware-based. The fact that they are never connected to the internet makes cold wallets more secure - however, that same fact makes them less convenient. In order for a digital currency transaction to be processed by a cold wallet, the pending transaction must be transferred to the off-network wallet, approved by the cryptocurrency owner (digitally signed with the private key), and then re-transferred to an Internet-connected device, which can then transmit the signed transaction to the intended blockchain network. An example of a popular hardware cold storage wallet is the Ledger Nano.
Given the tradeoff of security features versus convenience, cold wallets are a good choice for users who want to hold digital currencies without performing many transactions and for storing larger amounts of cryptocurrency.
Hierarchical Deterministic Wallet – HD Wallet
Almost all modern wallets are a form of Hierarchical Deterministic (HD) wallet, and as such, they support sophisticated features that allow them to manage multiple cryptocurrencies and assets with ease. They do this by generating a tree-like hierarchy of crypto keys, and then using those keys to allow users to conveniently transact with multiple different currencies and wallet accounts. HD Wallets derive all of these keys and associated blockchain addresses from a single master seed.
Because of the way that HD wallets automatically generate and use a large pool of unique keys and blockchain addresses to receive funds, they give crypto owners a level of privacy that legacy wallets can not offer. A major benefit of HD wallets is that it eliminates the need to generate these addresses yourself, which can become an issue when processing a lot of transactions.
Some people prefer to control the generation of these public/private keys themselves, and will often turn to a Mnemonic Code Utility.
What Is a Paper Wallet?
Paper wallets store printed forms of cryptocurrency encryption keys on paper, rather than keeping them in a software wallet. With a paper wallet, usually, the public and private encryption keys are generated once on a computer in the form of Quick Response (QR) codes, printed out, and then stored. Sometimes the network address used to receive payments - an alternative form of the public key QR code which takes the form of a string of alphanumeric characters - is also written on the paper.
Paper wallets have significant limitations. Most notably, paper wallets contain just one address that can be used to receive funds, in contrast to software wallets, which generate and manage many different wallet addresses. Having just one public address to receive funds limits privacy, since transactions on public blockchain networks can be observed, and correlated by the public address used. Another important aspect of paper wallets is that although receiving payments is straightforward, spending cryptocurrency from a paper wallet is much more complicated. To spend funds from a paper wallet, a software wallet must be used in combination, to perform the authorization step of approving the transaction. However, software wallets often move all unspent cryptocurrency "change" from that transaction into a different "change address" - an important detail for the paper wallet owner to anticipate and record, else they risk losing all of their remaining cryptocurrency. Paper wallets are generally considered to be outdated, and dangerous for new users to use.
Where do I get a wallet?
There are many software wallets available through cryptocurrency exchanges and app stores, and cryptocurrency news sites regularly publish updated reviews comparing wallet features and user satisfaction. There is a smaller set of choices for hardware wallets, which are available directly from vendors.
Never, ever buy a used hardware wallet, due to the risk of tampering - buy them only directly from the vendor or their authorized dealer, otherwise you may fall victim to a supply-chain attack, where post-manufacturing wallets are tampered with before being sold online.
Your decision about which type or brand of wallet to use should be based on your anticipated long-term usage patterns and security needs. Consider whether you intend to use just one crypto exchange or several, and similarly, which cryptocurrencies you may want to hold. Also consider your planned frequency of transacting, your risk tolerance for your chosen investment level, and your technical skill level.
There is no "right" crypto wallet for everyone. Many cryptocurrency investors start out using a custodial wallet, and later learn how to use a hardware wallet, practicing its use with a small number of funds - such a phased strategy limits risk while building knowledge and confidence. Having both a custodial and a non-custodial wallet may be a sensible longer-term plan for individual investment needs, where long-term holdings are kept in a hardware wallet, and a small amount of "spending crypto" can be kept in a hot wallet or exchange.
We have compiled guides of a selection of the most popular crypto wallets - and will be adding more in the future.
What do I need to do to make sure my wallet is safe and secure?
Even with the most secure wallet, you can lose all of your cryptocurrency if you lose your private key that controls the wallet. This can happen if you've lost access to your wallet (damaged/lost software or hardware) and you failed to successfully back up the necessary information to restore it. A wallet backup is performed by backing up your private key as a seed phrase. It is one of the most essential things to understand and learn in crypto. You can learn more about seed phrases in our article "What is a Seed phrase?"
"Secure" does not mean just protection from theft, but also protection against key management failures. Because the diversity of risks to crypto wallets is high, no matter which wallet type you choose, it is important to understand the set of risks associated with your personal choices.
Carefully following best practices in wallet configuration, limiting who can access your wallet, and seed phrase management are all critical to maintaining a secure digital wallet. Additionally, informing carefully-chosen friends or associates of crypto holding details can involve subjective and personal decisions.
Perfect security is not attainable, but with some thought, you can choose the "right" balance of security and risk for you, given your personal situation. For more information about wallet security, see the article "11 Things to Set Up a Safe Crypto Environment."
What is a Crypto Wallet?
Discover the differences between wallet types, and some of the functional and security tradeoffs between them.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
Vault12 is NOT a financial institution, cryptocurrency exchange, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys for the purpose of inheritance. We provide no legal or financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
Prepare for the future - Don't lose your crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
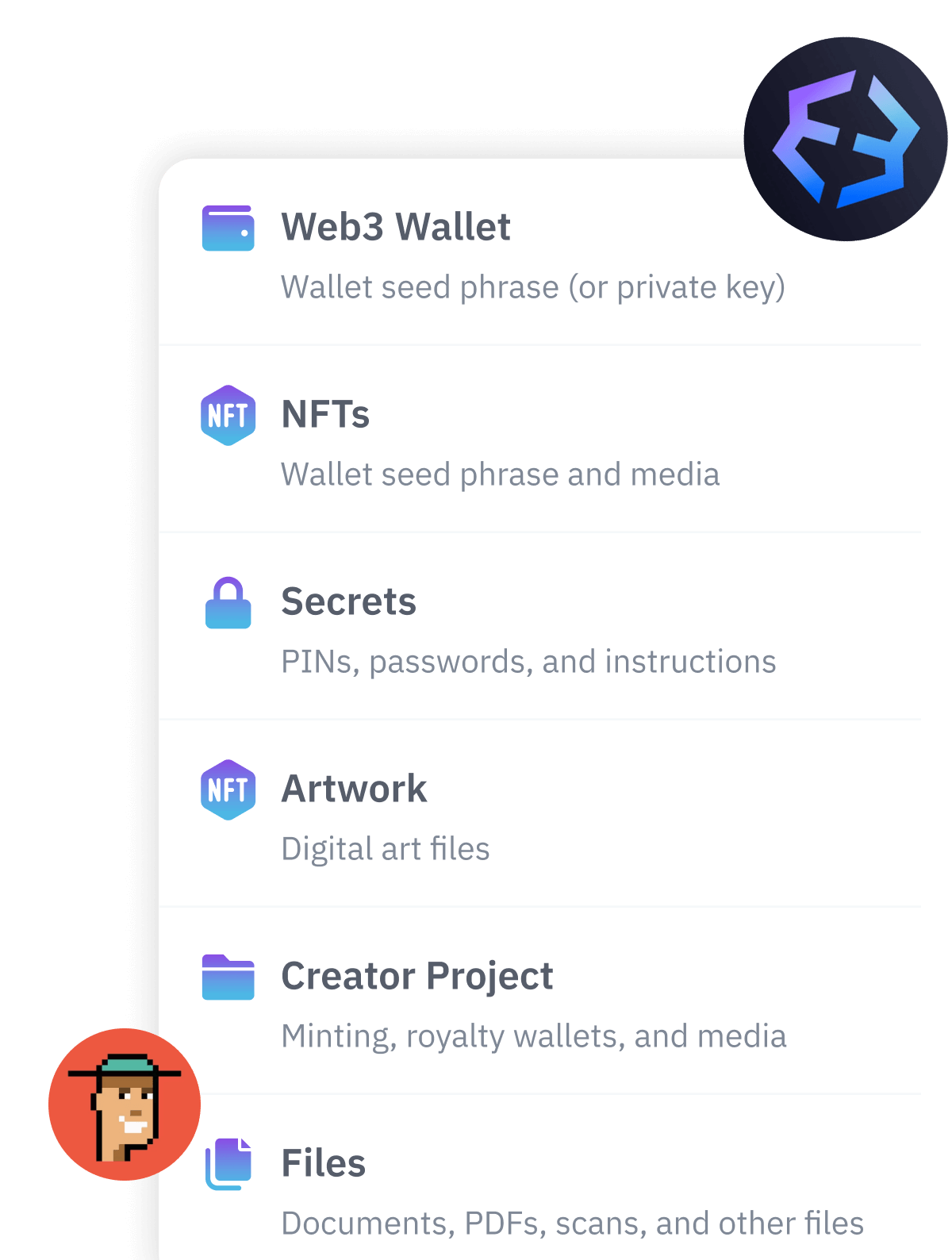
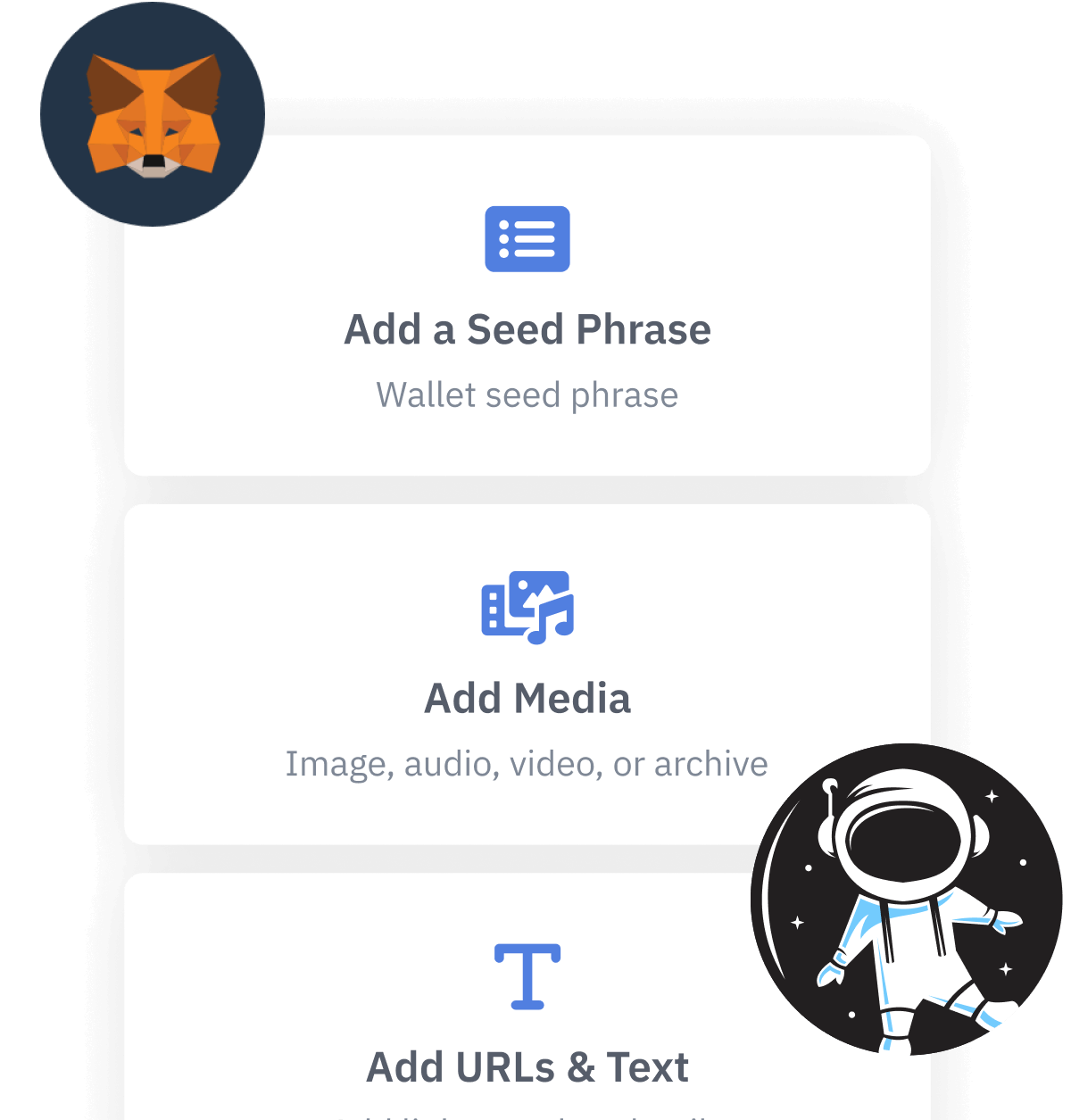
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.