Contents
- Privacy is important to crypto owners
- Blockchain addresses can identify you
- HD wallets offer "fresh" addresses every time
- Limit who has your Personally-Identifying Information
- Crypto exchanges know your Personally-Identifying Information
- Exchanges use "KYC" information for Anti-Money Laundering
- Privacy regulations offer limited protection
- You can acquire crypto anonymously
- You can spend crypto anonymously
- Crypto wallets that prioritize privacy
- Running your own Bitcoin node offers extra privacy
- "Privacy coins" may offer extra privacy
- Privacy Best Practices
- Diving deep into crypto privacy
Why does privacy matter?
Privacy is especially important for owners of digital assets - understand how to protect yours.
TL;DR
Keeping your crypto transactions private is important for your safety and confidentiality.
Be very careful who you share personal or financial information with.
Your personally-identifying information (PII) is a target for thieves.
"Know Your Customer" (KYC) information is collected by banks and many crypto-related service companies.
Public blockchain ledgers can be analyzed for clues about who controls which addresses.
HD wallets are recommended to generate a unique wallet address for each spend and receive transaction.
Privacy-enhancing wallets, strategies, and coins exist, but require at least an intermediate level of knowledge.
Bitcoin mixers offer an increasingly-popular way to gain privacy by combining together many users' unrelated transactions, then recording them on the blockchain as blended, more-anonymous transactions.
It is much easier to establish privacy of your crypto assets when you first buy them, rather than to make assets that are associated with you later look like they do not belong to you.
Privacy is important to crypto owners
It is easy for new crypto investors to overlook the importance of protecting their privacy when purchasing digital assets. At first, privacy may seem like a minor detail, since the initial purchase motivation may be just to "dip a toe into the crypto waters" with a nominal sum of money.
However, when you create an account on a crypto exchange, or start to use some other convenient "on-ramp" to crypto ownership, you are creating a digital footprint that can be attributed - by some party - to you. Once that footprint is established, you will likely be tempted to increase the size of your holdings by topping up your investment, or the value of your small investment might just skyrocket. Either way, an investment that you did not expect to be worth much suddenly could be worth a significant amount.
Although an increase in the value of your crypto holdings is great news, it reveals an important reason to be concerned about privacy from the very inception of your crypto journey: if anyone learns that you hold large sums of crypto, you are at risk of becoming a target of crime and theft. Privacy is important to cryptocurrency owners primarily because of the potentially high value that crypto holdings can have.
Privacy is also important because even for small crypto holdings, if your transactions are revealed to an audience that you did not intend, you could face potentially negative social impacts: you might use crypto to pay for sensitive products, financial accounts, or information subscriptions that you would rather not tell others about - in some cases, its discovery could make you a potential target for blackmail or harassment.
It is very difficult to restore privacy of crypto ownership after it has been attributed to you, and depending on how you choose to move existing digital assets, there may be profit-taking tax implications when you appear to be moving your crypto.
Smart crypto investors consider privacy before performing their very first transaction, no matter how you purchase your first digital assets.
Blockchain addresses can identify you
Anyone can track blockchain address transactions on public blockchain ledgers by analyzing transactions with a blockchain explorer such as Blockchain.info, etherscan.io, or solscan.io.
There are several ways that your crypto transactions could be identified as related: For example, if someone re-uses a blockchain address (like a single-address paper wallet), then all transactions that have been associated with that address can be identified as being linked to the same owner. Other types of transactions (like spending multiple tiny sums of crypto "dust" from different addresses at the same time) can also reveal connections between multiple addresses, showing that they are controlled by the same person or entity. Curious individuals, as well as professional companies specializing in blockchain analysis, puzzle together clues like these to gain more understanding and data about transactions.
Reused or associated addresses may reveal about the address owner:
- what companies the person bought from
- what causes they sent assets to
- what income was received
Observers may not immediately know who controls a given address, but some day, they may see a clue that allows them to identify who the owner is. For example, if you reuse an address that you have shared with someone like a service provider, they could know who you are, and could watch other transactions that you perform at that address.
If someone can identify you personally as connected with a blockchain address that has received large sums of money, you could be targeted for blackmail, kidnapping, theft, or any number of threats.
People or organizations with a known Bitcoin receive address could also be blacklisted: for example, a payment-related organization like Paypal could decide that they do not want to support transactions sent to a given address.
HD wallets offer "fresh" addresses every time
A popular type of crypto wallet that helps you to preserve your crypto privacy is a Hierarchical Deterministic (HD) wallet. HD wallets are designed to give you as many spending and receiving wallet addresses as you want - a fresh one every time, completely avoiding blockchain address reuse.
To retain your privacy when spending or receiving crypto, you should allow your HD wallet to provide you with a new Send or Receive address every time you perform a transaction.
To create many unique addresses, an HD wallet uses the wallet seed phrase to generate a master key pair: an extended private key (XPRIV) and an extended public key (XPUB). Then it can create many individual private and public keys that are hierarchically below the master ones. If you want to know more about XPUB addresses, swanbitcoin offers a nice explanation.
Your XPRIV should obviously always be protected, since it can be used to sign transactions and spend your crypto! Your XPUB also should be kept secret, since it allows read-only access to all of the "receive" addresses in your wallet - an XPUB can be used to configure a "watch-only" wallet. In fact, the Vault12 Digital Vault has an "Address Explorer" feature that can use an XPUB to build a watch-only wallet for you.
What you can and should share with others is a unique, freshly-created send or receive address that your HD wallet will generate for you every time you want to spend or accept crypto. By using a new address for each transaction, the "outside world" does not know which transactions are associated with a given wallet - each of the transactions appears on the public ledger to be independent.

An abstracted crypto transaction through a secure exchange
Limit who has your Personally-Identifying Information
Personally-Identifying Information (PII) is generally defined as any information or combination of information that could be used to identify you as an individual.
Common forms of PII include your name, government identification numbers (passport, drivers license, Social Security number, etc.), payment card numbers, birthday, physical address, email address, and telephone number. Even an IP address can be considered PII, although different countries have different privacy laws that vary on that point.
You should be very careful to only share your PII with reputable organizations, and only through secure, encrypted communication channels (like the main corporate https web site of the firms that you have chosen to work with). PII is a prime target of digital thieves. If your personal information were acquired by bad actors, it would be abused for fraudulent purposes, and then likely resold on the black market.
To protect your PII, be particularly wary of links in emails, since they are a common source of cleverly-crafted phishing attacks that target your PII. It is much safer to open your web browser and directly navigate to a reputable company's web site than to click on a link in an email, even if the email looks legitimate to you. Educate yourself and learn how to recognize and avoid being tricked by phishing attacks.
It is not directly related to crypto, but Facebook's ongoing challenges with leaked PII data demonstrate the high appetite for PII abuse - and keep in mind that PII attained from any source could be used to try to target crypto investors.
Exchanges, hardware wallet vendors, and all sorts of crypto-related firms are under constant attack as hackers try to steal PII. The hardware wallet vendor Ledger succumbed to one such high-profile attack in 2020, for which they had to issue a public apology.
Crypto exchanges know your Personally-Identifying Information
Cryptocurrency has a veneer of anonymity, but due to connections with financial accounts that are used to exchange currency for cryptocurrency in "on-ramp" crypto purchases and "off-ramp" crypto sales, your identity is often able to be associated with your crypto transactions. By default, your personally-identifying information is known to exchanges and to other crypto-related service providers with which you establish accounts. Pay attention to what information is solicited from you when you register for any services.
We are accustomed to trusting reputable organizations with our PII, and usually they do a good job of protecting it. But we should be conservative with our judgement of which organizations we give our information to, and should be aware that when we sign up to use a crypto exchange or other crypto-related service provider, they, as well as government regulatory entities, have the ability to associate our identity with crypto wallet addresses that we use.
Exchanges use "KYC" information for Anti-Money Laundering
You may wonder why you have to give your personal information to crypto exchanges.
Financial institutions and many crypto exchanges support governments in their enforcement of anti-money laundering (AML) regulations. When large sums of money or other assets are moved, governments have the right to scrutinize transactions to ensure that no money laundering or other criminal activity is underway. The acronym KYC stands for "Know Your Customer," and it is standard for banks and other financial institutions to require KYC information.
If you buy your crypto through a KYC-compliant exchange, you give up some privacy. However, if you do not buy your crypto through a KYC-compliant "on-ramp," governments tend to perceive transactions as less legitimate, since they do not know as much about the participants - as a result, there may be even more scrutiny of non-KYC transactions.
As crypto regulations evolve, there are personal choices to be made about tradeoffs with respect to privacy and perceived legitimacy. There is no "right" level of anonymity for your transactions, but you should be conscious of the level of privacy that you choose, and you should be conservative about which institutions and individuals you expose your information to.
Your currency-to-cryptocurrency transactions (crypto "on-ramps"), and your cryptocurrency-to-currency transactions (crypto "off-ramps") are some of the most important financial events that you will conduct. Be informed and cautious in which organizations you trust with an awareness of these transactions.
Privacy regulations offer limited protection
Different countries and municipal regions have varying privacy protection laws that offer you legal rights to control who can access or use your personally-identifying information, for what purposes, and for how long. Some of these laws include the European General Data Protection Regulation (GDPR), the U.S. Gramm-Leach-Bliley Act, the California Right to Financial Privacy Act, and the California Consumer Privacy Act.
However, you still have to provide your KYC information to major crypto exchanges if you want to do business with them, and it is still up to you to be conscious not to leave clues about your spending patterns on public-facing blockchain ledgers.
Additionally, there are significant privacy risks that regulations can not protect you from: unplanned problems such as cyber attacks, institutional misconfigurations, or insider leaks from exchanges.
You can acquire crypto anonymously
If you would like to maximize your crypto privacy, there are ways that you can acquire crypto that do not rely on KYC-compliant exchanges:
- Peer-to-peer trading platforms, which may use an escrow service to guarantee trouble-free payments.
- Crypto ATMs (although some require identification, and if you use a credit or debit card at them, you have lost any anonymity).
- Earning transaction fees as a crypto miner.
- Earning freelance income from customers who pay you in crypto. (Usually they would know who you are, but perhaps you provide services pseudonymously.)
You can spend crypto anonymously
The crypto world offers technology known as "mixers," or tumblers, which increase privacy by combining crypto coins from many sources and redistributing them in such a way that it is impossible to say which coins came from which origin. Similarly, a Bitcoin privacy improvement called CoinJoin increases privacy by producing multi-party transactions, rather than having all involved transactions identify which party performed transactions with which other party - in this way, it blurs the visible line of who actually transacted with whom for how much.
For Ethereum, there is a smart contract called Tornado that makes it harder to identify which tokens are being sent from which addresses. However, technologies such as Tornado are complex to use, and work best in the hands of "power users" who understand the nuances of timing and other techniques of obfuscation for their transactions. Additionally, the United States Treasury's Office for Foreign Assets Control has prohibited U.S. entities from using Tornado Cash.
Crypto wallets like Wasabi and Samourai are easier to use, and offer tumbling features that can help users leverage mixing technologies.
Regulators do not particularly like these forms of privacy protection, but they are becoming more widely used nonetheless by users seeking to keep their privacy as robust as possible.
Crypto wallets that prioritize privacy
A few crypto wallets specialize in providing features that support you in protecting your privacy. These wallets tend to have fast-changing feature sets as they implement new technologies like mixers.
Some high-privacy wallets are best for intermediate to advanced users. Privacy features are a little more complex to use than "default" transactions. Your wallet's documentation is the best place to learn more about the specific privacy features that are available to you.
To help you understand all of the choices among crypto wallets, Bitcoin.org offers you a handy interactive tool to compare features among many privacy-conscious wallets. (Keep the criterion checkbox "Privacy" checked.)
Running your own Bitcoin node offers extra privacy
If you run your own Bitcoin full node, you send your pending Bitcoin transactions to your own server to perform required checks against consensus rules, instead of sending them to a random node for those checks (which would reveal information about which transactions were requested from your IP address). Similarly, if your crypto wallet makes a request for your past transactions, your own full node could fulfill that request, rather than transmitting it to a random node for the information.
There are many guides about how to set up your own node to increase your privacy. Some wallet vendors provide instructions for how to run full nodes that integrate well with their products. Bitcoin.org offers a wealth of additional general information about how to get started with full nodes.
If you don't run your own full node, it is a good idea to use a VPN to obfuscate your IP address when you run crypto-related applications like your crypto wallet software.
"Privacy coins" may offer extra privacy
Privacy Coins are cryptocurrencies that are designed to keep transactional details private through various identity-cloaking mechanisms such as one-time addresses, ring signatures, and confidential transactions. There is much more to be considered than privacy when choosing which cryptocurrencies to invest in, but privacy features are a valid consideration.
Bitcoin used with CoinJoin can be considered to be a form of privacy coin. Altcoins that are making a name for themselves as privacy coins are Monero, Grin, Zcash, and Dash (which uses PrivateSend, an implementation of CoinJoin).
Privacy Best Practices
Privacy best practices include:
- Be conservative about which institutions you share your PII with.
- Keep quiet about your personal crypto holdings and use.
- Avoid blockchain address re-use.
Privacy advanced practices include:
- Run your own node.
- Purchase and sell crypto through anonymous platforms (brokered or peer-to-peer).
- Use coin-mixing wallet features.
Diving deep into crypto privacy
Crypto investors who want an extremely high level of privacy need to stay on top of multiple fast-changing technologies and services. No set of references will remain current or comprehensive for long, but these sites offer a wealth of further detail about options to secure the highest levels of privacy for your coins:
Why does privacy matter?
Privacy is especially important for owners of digital assets - understand how to protect yours.

Art Krotou
Art is a crypto-security expert and researcher with serial entrepreneurship background. Having a degree in physics and experiences in multiple cutting-edge industries like fintech, secure hardware and semiconductors, and identity gave him a unique multi-faceted perspective on the problem of key management for individuals in the crypto networks and the evolution of the internet in general.
In his current work, he is specifically researching how cryptographic keys can be inherited without posing a threat to 3rd parties in edge cases. In addition, he advocates for "fault-tolerance via secrets automation". He discusses the quantitative impact of user experience factors on the uptake of non-custodial solutions.
As one of his most notable accomplishments, he co-founded and led through the early years of the company that contributed to the complex technology behind Apple's recent M-series CPUs. He is also the creator of the most friendly and aesthetically pleasing, but nonetheless super secure and fault-tolerant hardware wallet - U•HODL.
Check out his curated series of "Vault12 Learn" contributions below, and follow him on Twitter and LinkedIn for more sharp insights.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
Vault12 is NOT a financial institution, cryptocurrency exchange, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys for the purpose of inheritance. We provide no legal or financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
You will lose your Bitcoin and other crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
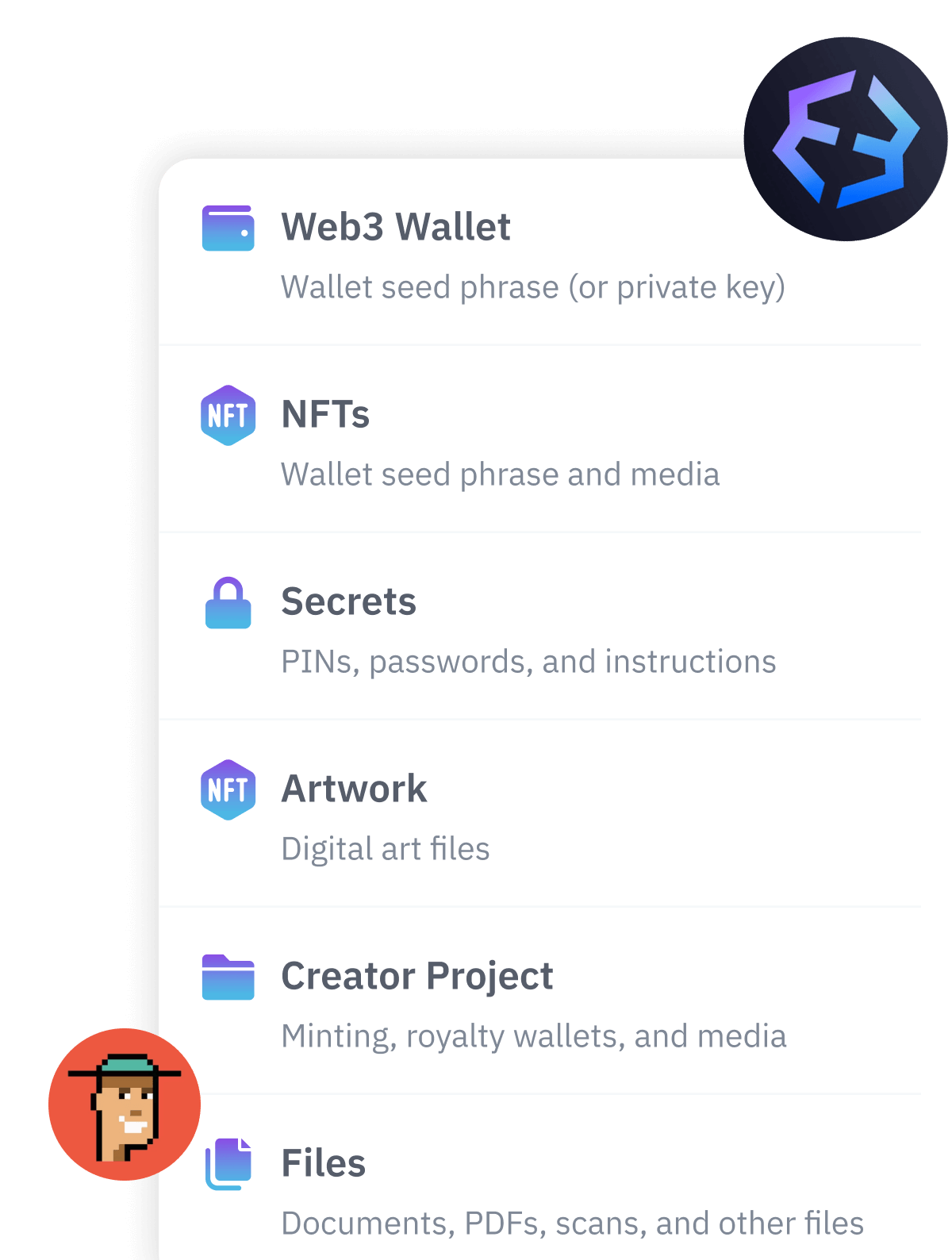
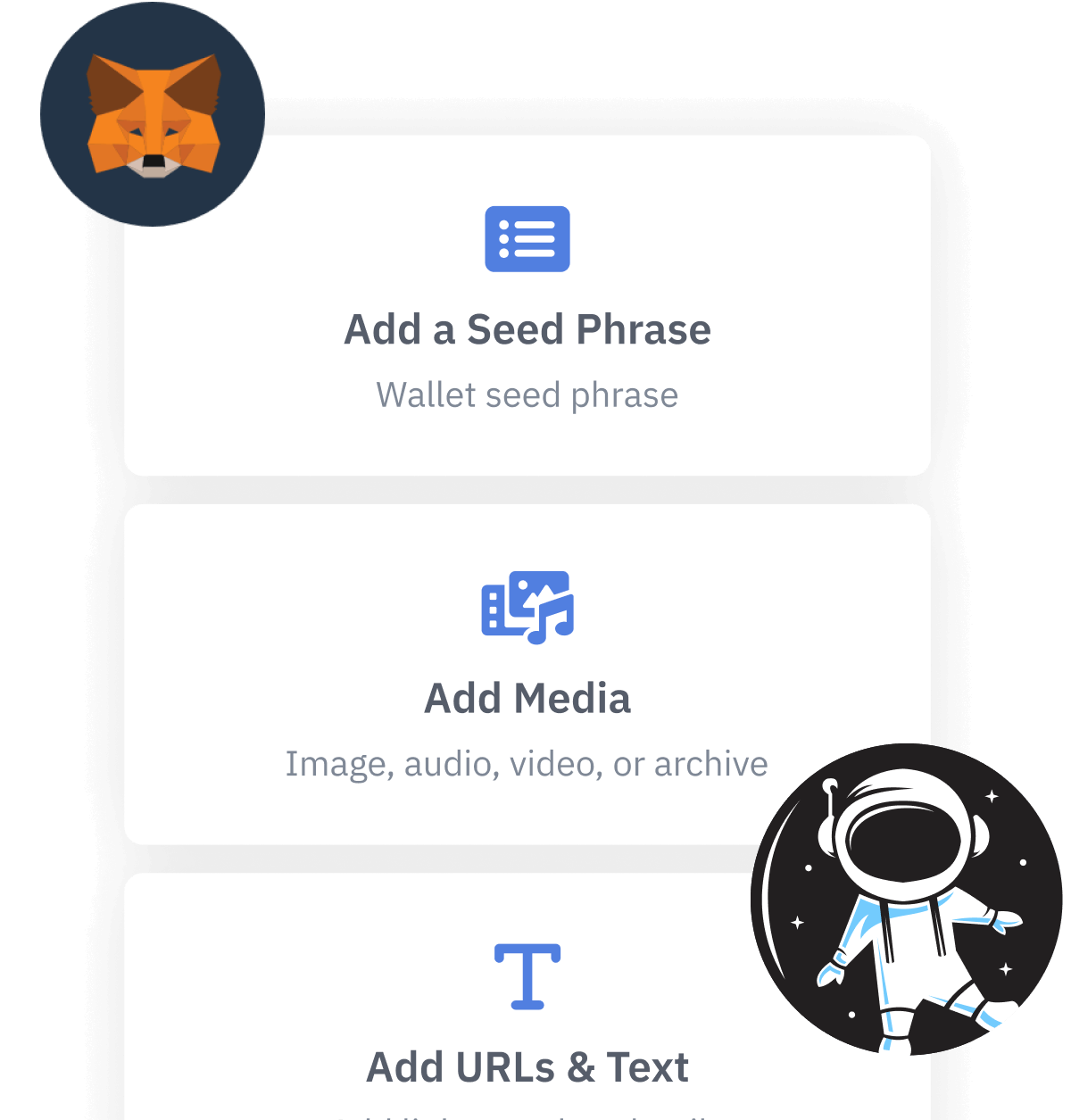
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.