Contents
- Key Points on How To Generate A Seed Phrase
- 1. How to generate a seed phrase with Vault12
- 2. How to generate a seed phrase with a calculator
- 3. How to generate a seed phrase with dice
- 4. How to generate a seed phrase with software crypto wallets
- 5. How to generate a seed phrase with hardware wallets
- What goes on behind the scenes of generating a seed phrase?
- How much entropy should your seed phrase have?
- How are SHA256 and BIP39 word lists used to generate a seed phrase?
- What are some different ways to perform Random Number Generation (RNG)?
- What are the security considerations of generating your own seed phrase?
How to generate a Seed Phrase.
Here are five ways to generate a seed phrase, with an in-depth discussion on the importance of randomness in ensuring security.
Your seed phrase is the very foundation of a modern digital wallet, and it is no exaggeration to say that seed phrases are at the heart of the cryptocurrency universe generally. But what is it? A seed phrase is a mnemonic code consisting of 12-24 words used to create or recover your crypto wallet. You may have heard it referred to as a backup phrase, recovery phrase, or mnemonic sentence.
Where do they come from? This article explains some common ways to generate seed phrases.
Key Points on How To Generate A Seed Phrase
When you have your own crypto wallet, you have a few choices for how to generate your seed phrase:
- The Vault12 Guard app can generate a secure seed phrase for you.
- You could let your digital wallet generate a seed phrase for you.
- Or for very high security, you could "roll your own" seed phrase with dice or a calculator as offline methods.
It is extremely important that your seed phrase be randomly generated, so that it cannot be guessed or reverse-engineered.
1. How to generate a seed phrase with Vault12
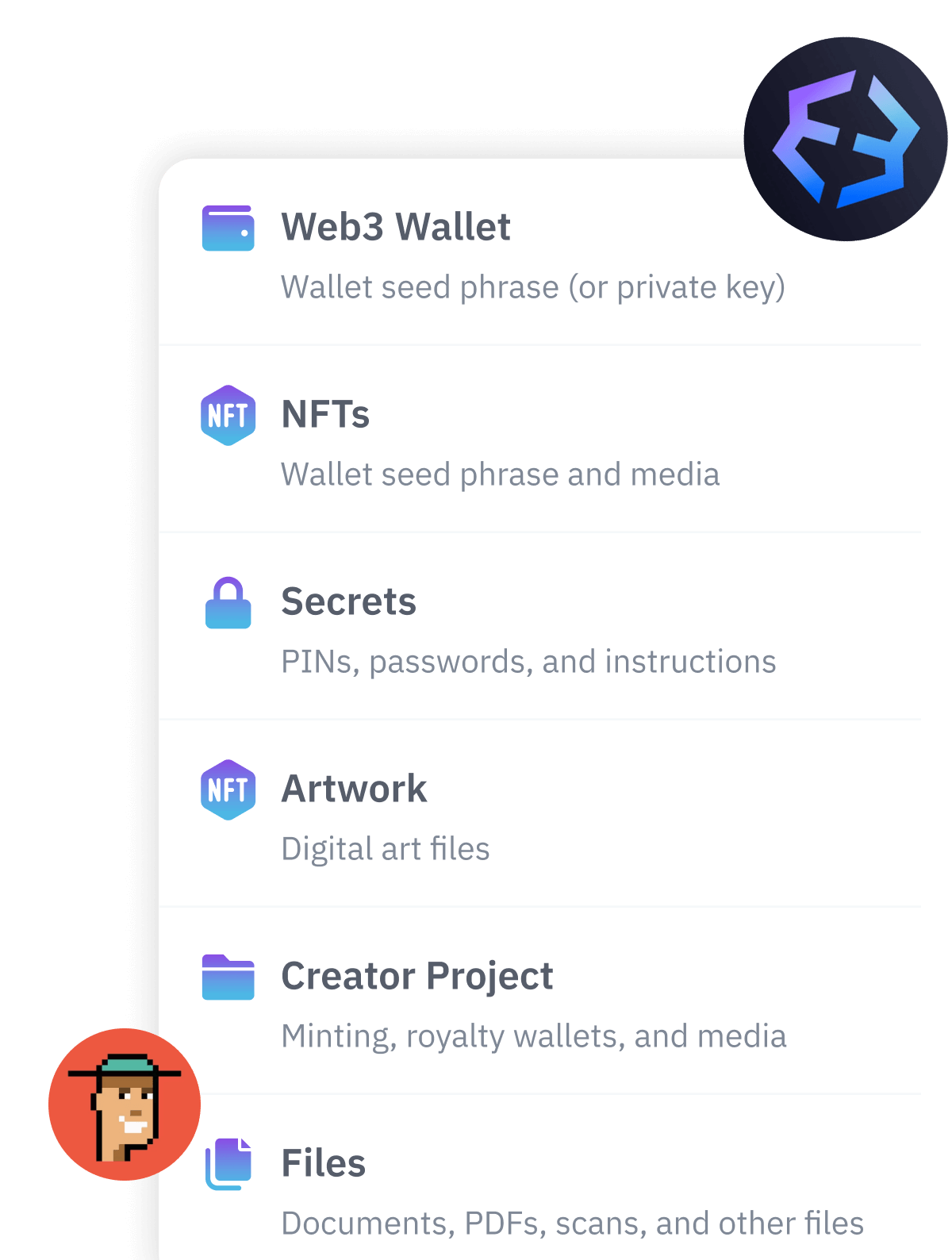
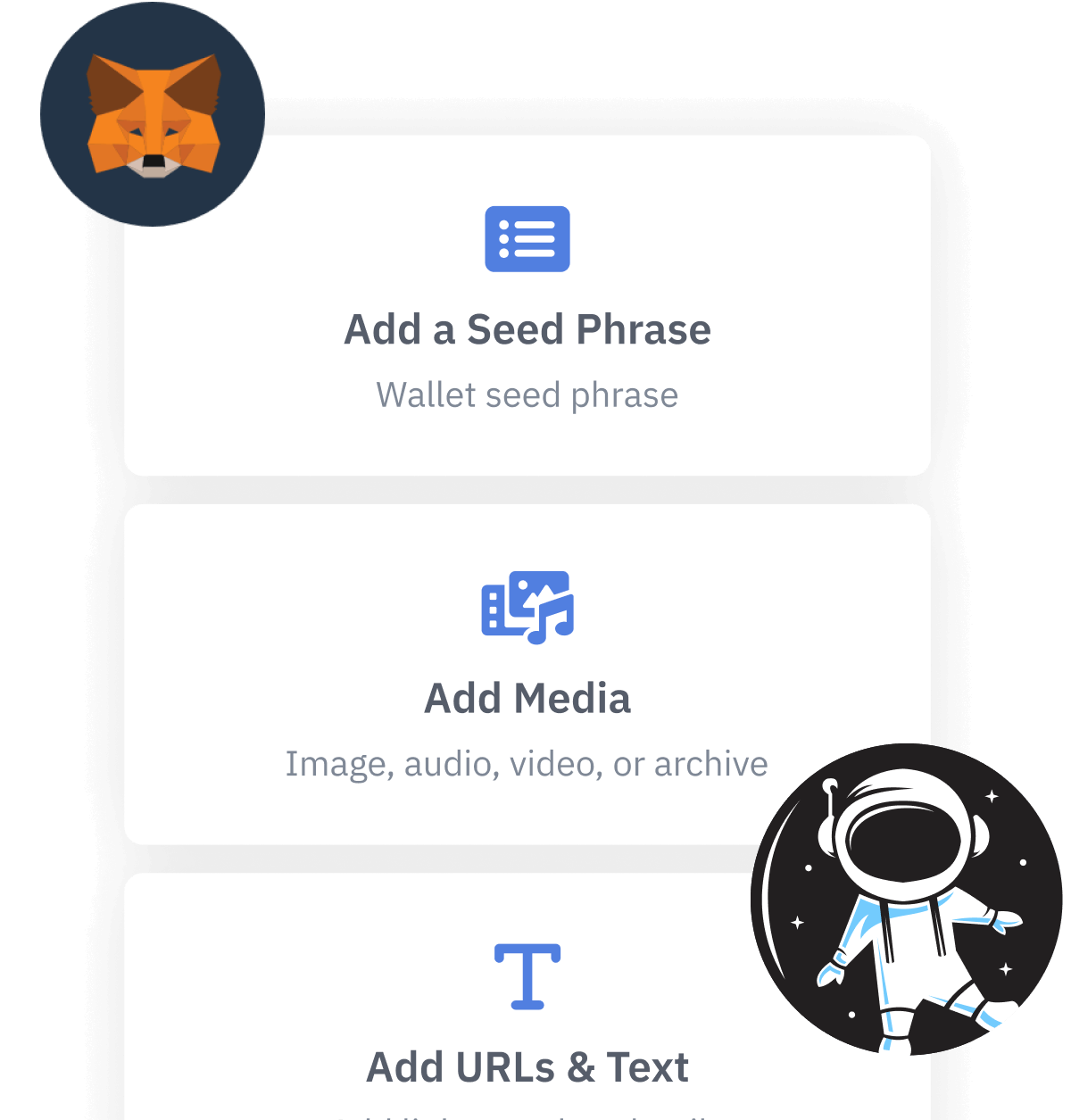
Vault12 can help you to easily create an encrypted and distributed digital vault. The Vault12 Guard app secures all sorts of digital assets including cryptocurrency seed phrases, and can also generate your seed phrase for you. You can be absolutely sure that your seed phrase is generated safely and automatically backed up in a secure manner. To learn more about it, please read our guide.
2. How to generate a seed phrase with a calculator
Generating a seed phrase by using a calculator is done offline, which requires a bit of extra effort but eliminates the risk of some classes of potential online attacks. This introduces a small number of new risks, however: instead of using one device to generate your seed phrase, you'll need to use two devices: the calculator and an air-gapped computer. To create a seed phrase this way, you'll need a calculator that has a RANDOM function (for generating entropy). Learn more about generating a seed phrase using an offline calculator here.
3. How to generate a seed phrase with dice
A humble pair of dice can be used for a non-digital and completely offline method of seed phrase generation. To do this, you'll need dice, a pen and paper, and the BIP39 word list. This method is not for the faint-hearted - be prepared to do some math! You can use a single die if you want, but it is recommended to use multiple dice. You'll be creating entropy by generating a large set of random numbers by using the dice. Learn how to generate a seed phrase with dice here.
4. How to generate a seed phrase with software crypto wallets
With very few exceptions, most modern wallets will create your seed phrase for you when you create your wallet. This process is usually automatic, with limited options for setting the parameters of your seed phrase. For most users this one-time approach is sufficient, and it won't be thought of again.
Please take a look at the article, "Using crypto wallets to generate seed phrases" to get an overview of how seed generation is done inside wallets during the set up phase.
Optionally refer to our Crypto Wallet Guides for step-by-step instructions on how specific wallets accomplish this.
Please keep in mind, that in any potentially high net-worth use case, generating seed phrases manually on your own - especially offline - is an excellent choice since it offers much higher security and greater control over the process.
5. How to generate a seed phrase with hardware wallets
Hardware wallets provide an extra level of security compared to software wallets, and provide methods to generate a seed phrase locally (within the wallet itself). Hardware wallets strike an excellent compromise between usability and high security. Feel free to check out Vault12's "How-to" wallet guides to bring you through the steps needed to securely generate and back up seed phrases using hardware wallets.
Here are some hardware wallets that we recommend:
- Ledger Nano X
- Ledger Nano S
- Trezor One
- Trezor Model T
- KeepKey
- ColdCard MK3
- BitBox 01/02
What goes on behind the scenes of generating a seed phrase?
In a nutshell, the process of generating a seed phrase starts with generating random data, called entropy. The entropy is then run through a hashing function - specifically SHA256 - to generate a checksum. Part of the checksum is then added to the random data. The resulting output is then split into chunks of 11 bits, where each 11-bit chunk maps to a single word on the BIP39 word list.
Confused about anything in the above paragraph? Don't worry, each step will be explained in an easy to understand format below. You can also get a higher-level understanding of seed phrase construction by checking out the article "What is BIP39?".
How much entropy should your seed phrase have?
Generating a seed phrase HAS to begin with a RANDOM SOURCE OF DATA, otherwise an attacker could possibly steal funds by guessing or regenerating your seed phrase. Entropy is a measure of how random a set of data is.
Which offers more randomness: rolling 1 die, or rolling 2 dice? Since 2 dice have more possible outcomes, the randomness is higher. It is the same for your seed phrase. The more words that are in your seed phrase, the higher the entropy.
To successfully generate a seed phrase, the entropy generated has to fit certain parameters. The random data must be between 128 bits and 256 bits of entropy, and divisible by 32.
128 bits of entropy maps to a 12 word seed phrase
160 bits of entropy maps to a 15 word seed phrase
192 bits of entropy maps to an 18 word seed phrase
224 bits of entropy maps to a 21 word seed phrase
256 bits of entropy maps to a 24 word seed phrase
How are SHA256 and BIP39 word lists used to generate a seed phrase?
A hash function is a computer program that takes an input of data and returns a verifiable result, called a checksum. The input can be any source of data. Running the same hash function again on the same input data will always return the same checksum as the result.
For example, running your randomized source data of 128 bits of entropy through a hash function will always return the same result, so it can be used as a checksum. If the source data changes, you will get a different result from the hash function.
In this step, the random source data is run through the SHA256 hash function. The first X digits of the checksum are then added to the random source data/entropy, where X is equal to: (amount of bits of entropy / 32).
256 bits of entropy (256/32 = 8) - add the first 8 bits of the checksum to the random data
224 bits of entropy (224/32 = 7) - add the first 7 bits of the checksum to the random data
192 bits of entropy (192/32 = 6) - add the first 6 bits of the checksum to the random data
160 bits of entropy (160/32 = 5) - add the first 5 bits of the checksum to the random data
128 bits of entropy 128/32 = 4) - add the first 4 bits of the checksum to the random data
It's important to note that BIP39 generates the seed phrase from binary code, which is made up of 0's and 1's. However, the SHA256 hash function returns the checksum as a sequence of numbers and letters, called a hexadecimal. So in order to get the seed phrase, you have to convert the checksum from hexadecimal format to binary format.
Here's the next step: We slice the result into 11-bit chunks of data. Each 11-bit chunk of data will map to a word from the BIP39 word list
You have seen the word "bit" used a few times in this article. A bit represents 0's and 1's. It is the smallest representation of data we have, and it is expressed in a language our computers understand.
Your original source of random data (or entropy) plus the SHA256 checksum is divisible by 11. The BIP39 word list contains 2048 words, and each word on the list maps to 11 bits of data. In this next step, you break your entropy+checksum combo into sequential chunks of 11 bits.
It is important that you slice the 11-bit chunks in sequential order. This means going from left to right, every 11 bits is grouped together. Every 11 bits represents a word in your seed phrase, and the order of the words has to be correct.
The next step is to convert your 11-bit sequence into decimal format. This will give you a number that maps to the BIP39 word list. Now, in the correct order, map each 11-bit sequence to the matching word in the BIP39 word list. Finally, this is your seed phrase!
It's important to highlight that some word lists for BIP39 might start with 1. In code, the first number is always 0. This means that 2048 words are listed as 0-2047, not 1-2048. If your BIP39 word list starts with 1 instead of 0, you will need to subtract 1 from the word list numbers to get the correct word.
What are some different ways to perform Random Number Generation (RNG)?
Going back to generating your initial source of randomness: Once you generate the needed entropy, the remaining process of getting the seed phrase is simply math and cryptography. In practice, this means that when generating a seed phrase, the initial source of entropy is both the most important step, and also the step in which you have the most control over the result.
There are many ways to generate entropy: flipping a coin, rolling dice, dealing a deck of cards, recording ambient sound, and many more. The goal here is to get as close to true randomness as possible. If you are using a process that is not sufficiently random, an attacker could possibly recreate your seed phrase.
In the following sections of this article, we will cover different approaches for how to generate entropy, and thus generate your seed phrase.
What are the security considerations of generating your own seed phrase?
Taking control over the generation of your seed phrase provides an opportunity to increase the entropy of your seed phrase, thus increasing the security of your entire wallet. This does not come without risks - a single mistake can result in a less secure wallet, or even lost funds.
When generating your own seed phrase, security must be top-of-mind throughout the whole process. The most crucial part of generating your seed phrase rests with the generation of entropy, which is the first step of generating your seed phrase.
Your seed phrase can have 12, 15, 18, 21, or 24 words. Remember that the more words in your seed phrase, the higher the entropy, which results in higher security. A correctly generated 24-word seed phrase will ALWAYS produce a wallet that is more secure than a 12-word seed phrase. Many wallets today only produce 12-word seed phrases in their built-in wallet creation workflow - and given today's technology, 12-word seed phrases are still very secure. But a key concept here is 'correctly generated.' The only parameter that can be changed is the source of entropy. This is very important because if the source of entropy is corrupted, an attacker could potentially regenerate your wallet and steal your funds.
Generating entropy can be done manually or with a computer. Both methods have pros and cons, but when generating entropy, care must be taken to ensure that the process is done correctly and is free from outside manipulation or observation.
One example of manually generating entropy would be flipping a coin. But if an attacker gives you a coin that is weighted slightly in favor of heads, your initial source of entropy will have been corrupted.
When using a computer to generate entropy, the attack vectors (or corruption attempts) could be both over the internet and physically in-person. The computer being used should not be connected to the internet, as that could offer an opportunity for attackers to compromise the process. However, even if the device was ever connected to the internet, it could allow the possibility for this process to be compromised.
Part of being in a security mindset means limiting opportunities available for bad actors. A device not connected to the internet is considered to be air-gapped, and an attacker generally would have to be physically present at the device to be successful at manipulating its entropy generation capabilities.
Lastly, if you don't have a spare device that you can airgap, don't worry - you could use a "live" Linux environment. Many Linux operating systems are able to be run off of a portable USB stick or flash drive. These are called `live` distributions and they're released with verification signatures, so you can easily verify that the operating system has not been tampered with. We recommend Tails OS - a portable OS that protects against surveillance and censorship. To run the operating system, just plug in the flash drive and boot it up. When you're done, simply remove the flash drive and return to your normal operating system. This very temporary lifecycle of a "live" Linux distribution reduces the window of opportunity for even the cleverest bad actor to access and compromise it.
How to generate a Seed Phrase.
Here are five ways to generate a seed phrase, with an in-depth discussion on the importance of randomness in ensuring security.

Art Krotou
Art is a crypto-security expert and researcher with serial entrepreneurship background. Having a degree in physics and experiences in multiple cutting-edge industries like fintech, secure hardware and semiconductors, and identity gave him a unique multi-faceted perspective on the problem of key management for individuals in the crypto networks and the evolution of the internet in general.
In his current work, he is specifically researching how cryptographic keys can be inherited without posing a threat to 3rd parties in edge cases. In addition, he advocates for "fault-tolerance via secrets automation". He discusses the quantitative impact of user experience factors on the uptake of non-custodial solutions.
As one of his most notable accomplishments, he co-founded and led through the early years of the company that contributed to the complex technology behind Apple's recent M-series CPUs. He is also the creator of the most friendly and aesthetically pleasing, but nonetheless super secure and fault-tolerant hardware wallet - U•HODL.
Check out his curated series of "Vault12 Learn" contributions below, and follow him on Twitter and LinkedIn for more sharp insights.

Vault12
Vault12 is the pioneer in crypto inheritance and backup. The company was founded in 2015 to provide a way to enable everyday crypto customers to add a legacy contact to their cry[to wallets. The Vault12 Guard solution is blockchain-independent, runs on any mobile device with biometric security, and is available in Apple and Google app stores.
Vault12 is NOT a financial institution, cryptocurrency exchange, or custodian. We do NOT hold, transfer, manage, or have access to any user funds, tokens, cryptocurrencies, or digital assets. Vault12 is exclusively a non-custodial information security and backup tool that helps users securely store their own wallet seed phrases and private keys for the purpose of inheritance. We provide no legal or financial services, asset management, transaction capabilities, or investment advice. Users maintain complete control of their assets at all times.
Prepare for the future - Don't lose your crypto when you die...
...unless you set up Crypto Inheritance today.
It's simple — if you don't worry about crypto inheritance, nobody else will — not your software or hardware wallet vendors, not your exchanges, and not your wealth managers. So it's up to you to think about how to protect the generational wealth you have created, and reduce the risks around passing that crypto wealth on to your family and heirs. What are the challenges with crypto inheritance?
- Crypto Wallets are difficult to use and do not offer crypto inheritance management. In fact, most of them tell you to write down your seed phrase on a piece of paper, which is practically useless.
- Some people back up their wallet seed phrases or private keys on paper, local devices like hardware wallets or USBs, or in the cloud. All of these options have severe drawbacks that range from hacking to accidental loss to disrupted cloud services.
- Software wallets operate on specific blockchains, yet your crypto assets span multiple blockchains. For inheritance to work, you must be able to manage inheritance across every blockchain — now and forever.
Pioneering Crypto Inheritance: Secure Quantum-safe Storage and Backup
Vault12 is the pioneer in Crypto Inheritance, offering a simple yet powerful way to designate a legacy contact and pass on your crypto assets—like Bitcoin (BTC), Ethereum (ETH) and Solana (SOL) —to future generations. Built for everyday users yet robust enough for the most seasoned crypto enthusiasts, Vault12 Guard ensures your wallet seed phrases and private keys are preserved in a fully self-sovereign manner, across all Blockchains.
At the heart of Vault12 Guard is quantum-resistant cryptography and a decentralized, peer-to-peer network of trusted Guardians. Your critical information is never stored in the cloud, on Vault12 servers, or even on local devices—dramatically reducing the risk of a single point of failure. By fusing a powerful software layer with the Secure Element of iOS devices (Secure Enclave) and Google devices (Strongbox), Vault12 Guard locks down your private keys against present and future threats.
Our innovative approach harnesses social recovery, enabling you to appoint one or more trusted individuals or mobile devices as Guardians. These Guardians collectively safeguard your protected seed phrases in a decentralized digital Vault—so there’s no need for constant lawyer updates or bulky paperwork. Should the unexpected happen, your chosen legacy contact can seamlessly inherit your crypto assets without compromising your privacy or security.
Preserve your digital wealth for generations to come with Vault12 Guard—the simplest, most secure way to manage crypto inheritance and backup.
Take the first step and back up your crypto wallets.
Designed to be used alongside traditional hardware and software crypto wallets, Vault12 Guard helps cryptocurrency owners back up their wallet seed phrases and private keys (assets) without storing anything in the cloud, or in any single location. This increases protection and decreases the risk of loss.
The first step in crypto Inheritance Management is making sure you have an up-to-date backup.
The Vault12 Guard app enables secure decentralized backups, and provides inheritance for all your seed phrases and private keys across any blockchain, including Bitcoin, Ethereum, and others, and for any crypto wallet.
Note: For anyone unfamiliar with cryptocurrencies, Vault12 refers to wallet seed phrases and private keys as assets, crypto assets, and digital assets. The Vault12 Guard app includes a software wallet that works alongside your Digital Vault. The primary purpose of this is to guard your Bitcoin (BTC) and Ethereum (ETH) wallet seed phrases, private keys, and other essential data, now and for future generations.